Product categories
- Application Security
- Automotive Cyber Security
- Cloud Access Security Broker
- Cloud Security
- Cyber Security Services
- Data Security
- Endpoint Security
- Forensics
- Governance Risk Management & Compliance
- Infrastructure Security
- Mobile Security
- Network Security
- Password Manager
- Patch Configuration and Management
- Secure File Transfer
- Secure Web Gateway
- Security Information and Event Management
- Security Training Software
- Unified Threat Management
- User Security
- VAPT
-
ProDiscover
Platform for identification of look-alike mail domains. Proactive detection of look-alike domains through 14 types of domain variations.ProDiscover
Platform for identification of look-alike mail domains. Proactive detection of look-alike domains through 14 types of domain variations. -
ProDMARC
Implement email authentication with PRODMARC
ProDMARC acts as the shield of any organisation from e-mail based spoofing attacks that impact your brand and hence, your revenues. ProDMARC helps improve customer and third party trust in your email.- Protect your brand against impersonation
- Gain visibility of your email activities
- Improve Deliverability of Email
- Generate actionable threat intelligence
ProDMARC
Implement email authentication with PRODMARC
ProDMARC acts as the shield of any organisation from e-mail based spoofing attacks that impact your brand and hence, your revenues. ProDMARC helps improve customer and third party trust in your email.- Protect your brand against impersonation
- Gain visibility of your email activities
- Improve Deliverability of Email
- Generate actionable threat intelligence
-
ProPATROL
Platform for facilitating employees to report phishing attacks. One-click reporter integrated with mailbox having incident analysis and ticketing capabilities.ProPATROL
Platform for facilitating employees to report phishing attacks. One-click reporter integrated with mailbox having incident analysis and ticketing capabilities. -
Prophaze – Native Cloud Security Platform k8s
Prophaze WAF secures your Web Assets from OWASP Top 10 Vulnerabilities by running both as SAAS and On Prem deployment. Prophaze First native cloud security platform. It will block all the attacks targeting your Web Application in cloud & go live in 15 minutes.Prophaze – Native Cloud Security Platform k8s
Prophaze WAF secures your Web Assets from OWASP Top 10 Vulnerabilities by running both as SAAS and On Prem deployment. Prophaze First native cloud security platform. It will block all the attacks targeting your Web Application in cloud & go live in 15 minutes. -
ProPHISH
Arm your employees against phishing attacks
ProPHISH is a highly effective simulation based solution for training and identifying employees of your organization, who might be susceptible to targeted Phishing Attacks. platform to help identify and train employees who are susceptible to targeted phishing.ProPHISH
Arm your employees against phishing attacks
ProPHISH is a highly effective simulation based solution for training and identifying employees of your organization, who might be susceptible to targeted Phishing Attacks. platform to help identify and train employees who are susceptible to targeted phishing. -
Reblaze WAAP
About Reblaze: Reblaze provides a complete, cloud-based, comprehensive and proactive protection shield for web platforms (websites/web applications/API), together with a command and control system. We offer an all-in-one private virtual cloud-based solution (VPC) that includes IPS/WAF, DoS/DDoS protection, BOT detection and exclusion, anti-scraping, CDN and more. As a result of our unique approach, we monitor and cleanse the traffic before it reaches our customers' websites, and we can easily work with existing security solutions. The service requires a five-minute setup, zero installation, a single DNS change and can be deployed even under an attack. Service can be stopped at any stage and with a Try and Buy period of 30 days. We're fully integrated with AWS, GCP, and Azure, being able to build our platform in the clients' environment, ensuring privacy, enhancing the cloud's latency and efficiency, and also, reducing costs of traffic.Reblaze WAAP
About Reblaze: Reblaze provides a complete, cloud-based, comprehensive and proactive protection shield for web platforms (websites/web applications/API), together with a command and control system. We offer an all-in-one private virtual cloud-based solution (VPC) that includes IPS/WAF, DoS/DDoS protection, BOT detection and exclusion, anti-scraping, CDN and more. As a result of our unique approach, we monitor and cleanse the traffic before it reaches our customers' websites, and we can easily work with existing security solutions. The service requires a five-minute setup, zero installation, a single DNS change and can be deployed even under an attack. Service can be stopped at any stage and with a Try and Buy period of 30 days. We're fully integrated with AWS, GCP, and Azure, being able to build our platform in the clients' environment, ensuring privacy, enhancing the cloud's latency and efficiency, and also, reducing costs of traffic. -
Red Team Assessments
$100.00Red Team engagements can demonstrate the risk posed by an APT (Advanced Persistent Threat). These types of comprehensive, complex security assessments are best used by companies looking to improve the security maturity of the organization.Red Team Assessments
Red Team engagements can demonstrate the risk posed by an APT (Advanced Persistent Threat). These types of comprehensive, complex security assessments are best used by companies looking to improve the security maturity of the organization. -
SCRUTINY SENSOR
Scrutiny predicts the true nature of files by emulating the static and dynamic behavior in a crypto caged environment and simultaneously training self-learning sensors at the same time to provide accurate verdicts along with detailed analysis in seconds. Our unique approach detects both known and unknown ransomware strains without any reliance on data engrams, centralized signature databases, etc. Also, this stands out as multi-tier, more innovative, and advanced than the other ransomware detection methods available.SCRUTINY SENSOR
Category: Cloud Security Data Security Email Security Endpoint Security Industrial Security Internet of Things Security Malware Detection and Analysis |Scrutiny predicts the true nature of files by emulating the static and dynamic behavior in a crypto caged environment and simultaneously training self-learning sensors at the same time to provide accurate verdicts along with detailed analysis in seconds. Our unique approach detects both known and unknown ransomware strains without any reliance on data engrams, centralized signature databases, etc. Also, this stands out as multi-tier, more innovative, and advanced than the other ransomware detection methods available. -
SecurDPS Connect
SecurDPS Connect allows users to develop customized templates which train the solution to detect and replace sensitive data with encrypted or tokenized data before that information is stored in the application or cloud service. These templates provide the mechanism to define what types of information are sensitive and guide the type of protection for each data field.SecurDPS Connect
SecurDPS Connect allows users to develop customized templates which train the solution to detect and replace sensitive data with encrypted or tokenized data before that information is stored in the application or cloud service. These templates provide the mechanism to define what types of information are sensitive and guide the type of protection for each data field. -
Secure Code Review
$100.00Secure Code reviews are an effective method for finding bugs that can be difficult or impossible to find during black box or grey box testing. Our team utilizes best-in-class code review tools to scan the full codebase followed by a deep manual examination for areas of critical importance.Secure Code Review
Secure Code reviews are an effective method for finding bugs that can be difficult or impossible to find during black box or grey box testing. Our team utilizes best-in-class code review tools to scan the full codebase followed by a deep manual examination for areas of critical importance. -
SecureTower
SecureTower is a 2 in 1 Solution: Data Leak Protection + Employee Monitoring. It's key features include: - Data leak protection - Staff efficiency and loyalty monitoring - Identification of potentially dangerous employees (risk analysis) - Business communications archive maintainingSecureTower
Category: Data Breach Protection Data Leakage Prevention Data Security File Content Security Secure File Transfer | SKU: STSecureTower is a 2 in 1 Solution: Data Leak Protection + Employee Monitoring. It's key features include: - Data leak protection - Staff efficiency and loyalty monitoring - Identification of potentially dangerous employees (risk analysis) - Business communications archive maintaining -
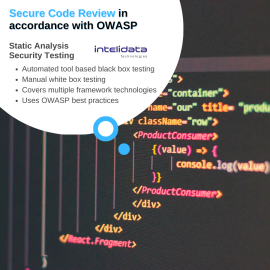
Static Analysis Security Testing by Intelidata
Static Analysis Security Testing (SAST) services by Intelidata to support developers in writing secure code and ensure application security. Secure Code Review is performed in accordance with Open Web Application Security Project (OWASP) industry best practice guidelines. At minimum, security assessment must include OWASP Top 10 security risk. Techniques to secure code review:- Automated tool based/ Black Box: In this approach, the secure code review is done using different open source/commercial tools.
- Manual/ White Box: The automatic tool scanner flags the whole code with vulnerabilities based on its perception. Thus a manual / white box testing is required.
Static Analysis Security Testing by Intelidata
Static Analysis Security Testing (SAST) services by Intelidata to support developers in writing secure code and ensure application security. Secure Code Review is performed in accordance with Open Web Application Security Project (OWASP) industry best practice guidelines. At minimum, security assessment must include OWASP Top 10 security risk. Techniques to secure code review:- Automated tool based/ Black Box: In this approach, the secure code review is done using different open source/commercial tools.
- Manual/ White Box: The automatic tool scanner flags the whole code with vulnerabilities based on its perception. Thus a manual / white box testing is required.
-
T2 COMMUNICATOR
$999.00T2 COMMUNICATOR secures mobile communication and data-at-rest. Engineered for organizations operating in the critical sectors. T2 COMMUNICATOR covers all critical vectors of attack:- hardware
- OS
- applications
- connectivity
T2 COMMUNICATOR
Category: Data-at-Rest Encryption Data-in-Motion Encryption Endpoint Security Messaging Security Mobile Communication Security Mobile Data Protection Mobile Device Management Secure File Transfer Zero trust |T2 COMMUNICATOR secures mobile communication and data-at-rest. Engineered for organizations operating in the critical sectors. T2 COMMUNICATOR covers all critical vectors of attack:- hardware
- OS
- applications
- connectivity
-
TDMARC – ThreatCop DMARC
TDMARC is an anti-spoofing and email authentication solution that helps organizations secure their outbound email flow and prevent the misuse of their email domain while boosting email deliverability and engagement rates.TDMARC – ThreatCop DMARC
TDMARC is an anti-spoofing and email authentication solution that helps organizations secure their outbound email flow and prevent the misuse of their email domain while boosting email deliverability and engagement rates. -
Thick Client VAPT
$110.00Thick client applications are generally more complicated and customized than web or mobile applications, so they need a specific approach when it comes to a penetration test. Our team discovers what technology is being used at client and server end, figures out application functionality and behavior, identify all entry points for user input, understand the core security mechanisms, and then proceed to find vulnerabilities.Thick Client VAPT
Thick client applications are generally more complicated and customized than web or mobile applications, so they need a specific approach when it comes to a penetration test. Our team discovers what technology is being used at client and server end, figures out application functionality and behavior, identify all entry points for user input, understand the core security mechanisms, and then proceed to find vulnerabilities. -
TPIR – ThreatCop Phishing Incident Response
TPIR is an email threat checker and a phishing incident response solution that empowers your employees to proactively detect and report suspicious emails, reducing the risk of email-based cyber threats.TPIR – ThreatCop Phishing Incident Response
TPIR is an email threat checker and a phishing incident response solution that empowers your employees to proactively detect and report suspicious emails, reducing the risk of email-based cyber threats.