Onefede > Products > Security Information and Event Management > Threat Intelligence and Signature Feeds
Product categories
- Application Security
- Automotive Cyber Security
- Cloud Access Security Broker
- Cloud Security
- Cyber Security Services
- Data Security
- Endpoint Security
- Forensics
- Governance Risk Management & Compliance
- Infrastructure Security
- Mobile Security
- Network Security
- Password Manager
- Patch Configuration and Management
- Secure File Transfer
- Secure Web Gateway
- Security Information and Event Management
- Security Training Software
- Unified Threat Management
- User Security
- VAPT
-
Brand Protection by Foresiet
Continuous brand scan helps to protect from Impersonation, Phishing, Rogue website, Fake social media accounts, pages, mobile application etc.
Stay protected against counterfeiters and unauthorized replicas, while also being proactive in spotting and preventing phishing scams.
Brand Protection by Foresiet
Continuous brand scan helps to protect from Impersonation, Phishing, Rogue website, Fake social media accounts, pages, mobile application etc.
Stay protected against counterfeiters and unauthorized replicas, while also being proactive in spotting and preventing phishing scams.
-
DARKBEAST
DARKBEAST provides incident responders, threat hunters, investigators, and intelligence analyst with a robust technology to dive into the cybercrime underground and investigate through KELA’s dark web data lake. Gain Visibility into the underground operations and stay ahead of attackers, all while maintaining anonymity and abiding by any security restrictionsDARKBEAST
Category: Digital Risk Monitoring Specialized Threat Analysis and Protection Threat Intelligence and Signature Feeds |DARKBEAST provides incident responders, threat hunters, investigators, and intelligence analyst with a robust technology to dive into the cybercrime underground and investigate through KELA’s dark web data lake. Gain Visibility into the underground operations and stay ahead of attackers, all while maintaining anonymity and abiding by any security restrictions -
INTELACT
INTELACT offers organizations a fully automated and targeted solution for Attack Surface Monitoring, enabling tailored configuration of client’s assets, automated monitoring of these assets in KELA’s Dark Net sources, and real-time alerting on any compromise or exposure of themINTELACT
INTELACT offers organizations a fully automated and targeted solution for Attack Surface Monitoring, enabling tailored configuration of client’s assets, automated monitoring of these assets in KELA’s Dark Net sources, and real-time alerting on any compromise or exposure of them -
ISMAC SOAR
$29.99$25.99 / year with a 14-day free trial and a $6,000.00 sign-up feeFor large and complex environments ISMAC SOAR will enable your team to achieve scalability of your cyberdefense efforts.ISMAC SOAR
Category: Cloud Security Compliance Management Container Security Log Management Malware Detection and Analysis Security Incident Management and Response SOAR Threat Intelligence and Signature Feeds VAPT | SKU: 003For large and complex environments ISMAC SOAR will enable your team to achieve scalability of your cyberdefense efforts.$25.99Was $29.99Save $4 -
RADARK
KELA’s RADARK delivers automated threat intelligence, cultivating the targeted and contextualized insights – at scale – that you need to stay ahead of attackers. Automatically monitor your environment and ensure that targeted threats are mitigated immediately to consistently maintain a strong security posture.RADARK
KELA’s RADARK delivers automated threat intelligence, cultivating the targeted and contextualized insights – at scale – that you need to stay ahead of attackers. Automatically monitor your environment and ensure that targeted threats are mitigated immediately to consistently maintain a strong security posture. -
Securaa – Security Automation Platform
Securaa is a Comprehensive No Code Security Automation Platform that blends intelligence, risk-based asset management, vulnerability insights, automation and incident response into a single platform enabling SOC’s to reduce cybersecurity response time significantly and increase throughput manifolds.- Best RoI in the industry
- Reduce response time by over 95%
- Increase productivity by 300%
- Automate 100% L1 tasks
- Implement in weeks
- Build new playbook in hours
Securaa – Security Automation Platform
Securaa is a Comprehensive No Code Security Automation Platform that blends intelligence, risk-based asset management, vulnerability insights, automation and incident response into a single platform enabling SOC’s to reduce cybersecurity response time significantly and increase throughput manifolds.- Best RoI in the industry
- Reduce response time by over 95%
- Increase productivity by 300%
- Automate 100% L1 tasks
- Implement in weeks
- Build new playbook in hours
-
SOCRadar Cyber Intelligence
SOCRadar provides actionable and contextualized intelligence aiming for security teams to operate efficiently. Our platform’s end-to-end automation supports SOC teams in dealing with manual and repetitive tasks that simultaneously minimize zero positives so that security analysts should focus on higher-impact projects. With SOCRadar’s early-warning system that detects attacks in the pre-exploit period, getting ahead of cyber attackers is now possible. Challenged by the understaffed teams, security leaders can effectively use SOCRadar as an extension to SOC teams.SOCRadar Cyber Intelligence
SOCRadar provides actionable and contextualized intelligence aiming for security teams to operate efficiently. Our platform’s end-to-end automation supports SOC teams in dealing with manual and repetitive tasks that simultaneously minimize zero positives so that security analysts should focus on higher-impact projects. With SOCRadar’s early-warning system that detects attacks in the pre-exploit period, getting ahead of cyber attackers is now possible. Challenged by the understaffed teams, security leaders can effectively use SOCRadar as an extension to SOC teams. -
Threat Hunting Services by SecurDefense
$7,500.00Cyber Attacks have become sophisticated than ever before. Organizations are challenged with proactively detecting the attacks, respond and timely mitigation. Typically Organizations deploy Security platforms like firewalls, Intrusion Detection / Preventions etc. However, attackers use new techniques and hide the attack below normal protocol and operations. Not only that, they dynamically keep changing the attack landscape and attack delivery methods. In this advance Technical exercise, we will use Threat intelligence and SIEM (Security Information and Event Management technologies to detect variety of threats.Threat Hunting Services by SecurDefense
Cyber Attacks have become sophisticated than ever before. Organizations are challenged with proactively detecting the attacks, respond and timely mitigation. Typically Organizations deploy Security platforms like firewalls, Intrusion Detection / Preventions etc. However, attackers use new techniques and hide the attack below normal protocol and operations. Not only that, they dynamically keep changing the attack landscape and attack delivery methods. In this advance Technical exercise, we will use Threat intelligence and SIEM (Security Information and Event Management technologies to detect variety of threats. -
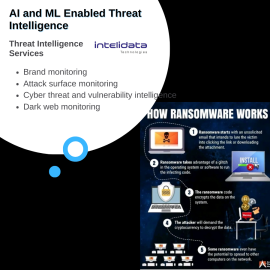
Threat Intelligence Services by Intelidata
Intelidata provides advanced threat intelligence with 360 degree coverage. The coverage includes:- Brand monitoring
- Social media monitoring
- Attack surface monitoring
- Cyber threat and vulnerability intelligence
- Cyber crime and dark web monitoring
- Supplier risk monitoring
Threat Intelligence Services by Intelidata
Intelidata provides advanced threat intelligence with 360 degree coverage. The coverage includes:- Brand monitoring
- Social media monitoring
- Attack surface monitoring
- Cyber threat and vulnerability intelligence
- Cyber crime and dark web monitoring
- Supplier risk monitoring