Product categories
- Application Security
- Automotive Cyber Security
- Cloud Access Security Broker
- Cloud Security
- Cyber Security Services
- Data Security
- Endpoint Security
- Forensics
- Governance Risk Management & Compliance
- Infrastructure Security
- Mobile Security
- Network Security
- Password Manager
- Patch Configuration and Management
- Secure File Transfer
- Secure Web Gateway
- Security Information and Event Management
- Security Training Software
- Unified Threat Management
- User Security
- VAPT
-
Appknox Static Application Security Testing
Simplified Static Application Security Testing (SAST) for Mobile App Security- Surface vulnerabilities before they turn into a threat
- Don’t let security become an unpredictable blocker when you go to market
- Integrate security as a regular part of your development cycle without shifting existing practices
Appknox Static Application Security Testing
Simplified Static Application Security Testing (SAST) for Mobile App Security- Surface vulnerabilities before they turn into a threat
- Don’t let security become an unpredictable blocker when you go to market
- Integrate security as a regular part of your development cycle without shifting existing practices
-
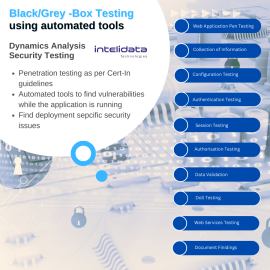
Dynamic Analysis Security Testing by Intelidata
Static Analysis Security Testing (SAST) services by Intelidata helps in finding vulnerabilities in the application while it is running. •Black/Grey-box security testing using automated tools; examines an application as it's running to find vulnerabilities that an attacker could exploit. •DAST will help in picking out deployment specific issues •Results from DAST and SAST can be compared to weed out false positivesDynamic Analysis Security Testing by Intelidata
Static Analysis Security Testing (SAST) services by Intelidata helps in finding vulnerabilities in the application while it is running. •Black/Grey-box security testing using automated tools; examines an application as it's running to find vulnerabilities that an attacker could exploit. •DAST will help in picking out deployment specific issues •Results from DAST and SAST can be compared to weed out false positives -
Indusface Web Application Scanner
Comprehensive, In-Depth & Managed Application Security Testing Indusface WAS Premium is offered as a SaaS-based solution, and provides real-time reports and summaries based on type and severity of vulnerabilities through the dashboard. It is designed to help organizations manage security across multiple web applications with daily or on-demand auditing, defacement protection and blacklisting detection Indusface WAS Premium provides comprehensive dynamic application security testing (DAST). It combines automated web application scanning to detect OWASP Top 10 and malwares along with CERT-In certified security expert validation for comprehensive analysis on business logic flaws and other complex vulnerabilities. Our managed security team also provides in-depth verification and demonstration of business impacts of the complex vulnerabilities.Indusface Web Application Scanner
Comprehensive, In-Depth & Managed Application Security Testing Indusface WAS Premium is offered as a SaaS-based solution, and provides real-time reports and summaries based on type and severity of vulnerabilities through the dashboard. It is designed to help organizations manage security across multiple web applications with daily or on-demand auditing, defacement protection and blacklisting detection Indusface WAS Premium provides comprehensive dynamic application security testing (DAST). It combines automated web application scanning to detect OWASP Top 10 and malwares along with CERT-In certified security expert validation for comprehensive analysis on business logic flaws and other complex vulnerabilities. Our managed security team also provides in-depth verification and demonstration of business impacts of the complex vulnerabilities. -
Mobile Application Penetration Testiing
$110.00Our mobile security testing services combine static and behavioral analysis to deliver full visibility into flaws in applications in real-time. Our services are easy to use and highly accurate, helping to avoid false positives and providing step-by-step guidance to remediate vulnerabilities found during security testing. With our services, development teams can meet the demands of regulatory frameworks more quickly and with less effort.Mobile Application Penetration Testiing
Our mobile security testing services combine static and behavioral analysis to deliver full visibility into flaws in applications in real-time. Our services are easy to use and highly accurate, helping to avoid false positives and providing step-by-step guidance to remediate vulnerabilities found during security testing. With our services, development teams can meet the demands of regulatory frameworks more quickly and with less effort. -
Red Team Assessments
$100.00Red Team engagements can demonstrate the risk posed by an APT (Advanced Persistent Threat). These types of comprehensive, complex security assessments are best used by companies looking to improve the security maturity of the organization.Red Team Assessments
Red Team engagements can demonstrate the risk posed by an APT (Advanced Persistent Threat). These types of comprehensive, complex security assessments are best used by companies looking to improve the security maturity of the organization. -
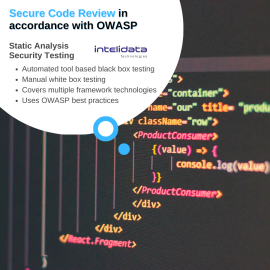
Secure Code Review
$100.00Secure Code reviews are an effective method for finding bugs that can be difficult or impossible to find during black box or grey box testing. Our team utilizes best-in-class code review tools to scan the full codebase followed by a deep manual examination for areas of critical importance.Secure Code Review
Secure Code reviews are an effective method for finding bugs that can be difficult or impossible to find during black box or grey box testing. Our team utilizes best-in-class code review tools to scan the full codebase followed by a deep manual examination for areas of critical importance. -
Static Analysis Security Testing by Intelidata
Static Analysis Security Testing (SAST) services by Intelidata to support developers in writing secure code and ensure application security. Secure Code Review is performed in accordance with Open Web Application Security Project (OWASP) industry best practice guidelines. At minimum, security assessment must include OWASP Top 10 security risk. Techniques to secure code review:- Automated tool based/ Black Box: In this approach, the secure code review is done using different open source/commercial tools.
- Manual/ White Box: The automatic tool scanner flags the whole code with vulnerabilities based on its perception. Thus a manual / white box testing is required.
Static Analysis Security Testing by Intelidata
Static Analysis Security Testing (SAST) services by Intelidata to support developers in writing secure code and ensure application security. Secure Code Review is performed in accordance with Open Web Application Security Project (OWASP) industry best practice guidelines. At minimum, security assessment must include OWASP Top 10 security risk. Techniques to secure code review:- Automated tool based/ Black Box: In this approach, the secure code review is done using different open source/commercial tools.
- Manual/ White Box: The automatic tool scanner flags the whole code with vulnerabilities based on its perception. Thus a manual / white box testing is required.
-
Thick Client VAPT
$110.00Thick client applications are generally more complicated and customized than web or mobile applications, so they need a specific approach when it comes to a penetration test. Our team discovers what technology is being used at client and server end, figures out application functionality and behavior, identify all entry points for user input, understand the core security mechanisms, and then proceed to find vulnerabilities.Thick Client VAPT
Thick client applications are generally more complicated and customized than web or mobile applications, so they need a specific approach when it comes to a penetration test. Our team discovers what technology is being used at client and server end, figures out application functionality and behavior, identify all entry points for user input, understand the core security mechanisms, and then proceed to find vulnerabilities. -
Web Application Penetration Testing
$110.00Web application security testing is critical to protecting both your apps and your organization. Your web applications are likely to be the #1 attack vector for malicious individuals seeking to breach your security defenses. Available to users 24/7, web apps are the easiest target for hackers seeking access to confidential back-end data.Web Application Penetration Testing
Web application security testing is critical to protecting both your apps and your organization. Your web applications are likely to be the #1 attack vector for malicious individuals seeking to breach your security defenses. Available to users 24/7, web apps are the easiest target for hackers seeking access to confidential back-end data. -
Web Application Security Penetration Testing
Effective security testing protects your apps from cyber-threats and vulnerabilities
From online and mobile apps to platform and hardware-hosted programs, Kratikal's application security testing services help you address application vulnerabilities while minimizing technological risks to meet regulatory compliance. Our Application Security Methodology goes beyond software detection to identify and prioritize the most vulnerable areas of your online application, as well as offer real solutions.Web Application Security Penetration Testing
Effective security testing protects your apps from cyber-threats and vulnerabilities
From online and mobile apps to platform and hardware-hosted programs, Kratikal's application security testing services help you address application vulnerabilities while minimizing technological risks to meet regulatory compliance. Our Application Security Methodology goes beyond software detection to identify and prioritize the most vulnerable areas of your online application, as well as offer real solutions.