Description
Penetration Testing
Penetration testing is the process of hacking a system with the permission from the owner of that system, to evaluate security, Hack Value, Target of Evaluation (TOE), attacks, exploits, zero-day vulnerability & other components such as threats, vulnerabilities, and daisy chaining. We perform Penetration Testing as per Cert-in guidelines.
Types of Penetration Testing
Three types of Penetration testing are important to be differentiated because a penetration tester may have asked to perform any of them.
Black Box
The black box is a type of penetration testing in which the pentester is blind testing or double-blind testing, i.e. provided with no prior knowledge of the system or any information of the target. Black boxing is designed to demonstrate an emulated situation as an attacker in countering an attack.
Grey box
Grey box, is a type of penetration testing in which the pentester has very limited prior knowledge of the system or any information of targets such as IP addresses, Operating system or network information in very limited. Grey boxing is designed to demonstrate an emulated situation as an insider might have this information and to counter an attack as the pentester has basic, limited information regarding target.
White box
The white box is a type of penetration testing in which the pen tester has complete knowledge of system and information of the target. This type of penetration is done by internal security teams or security audits teams to perform auditing.
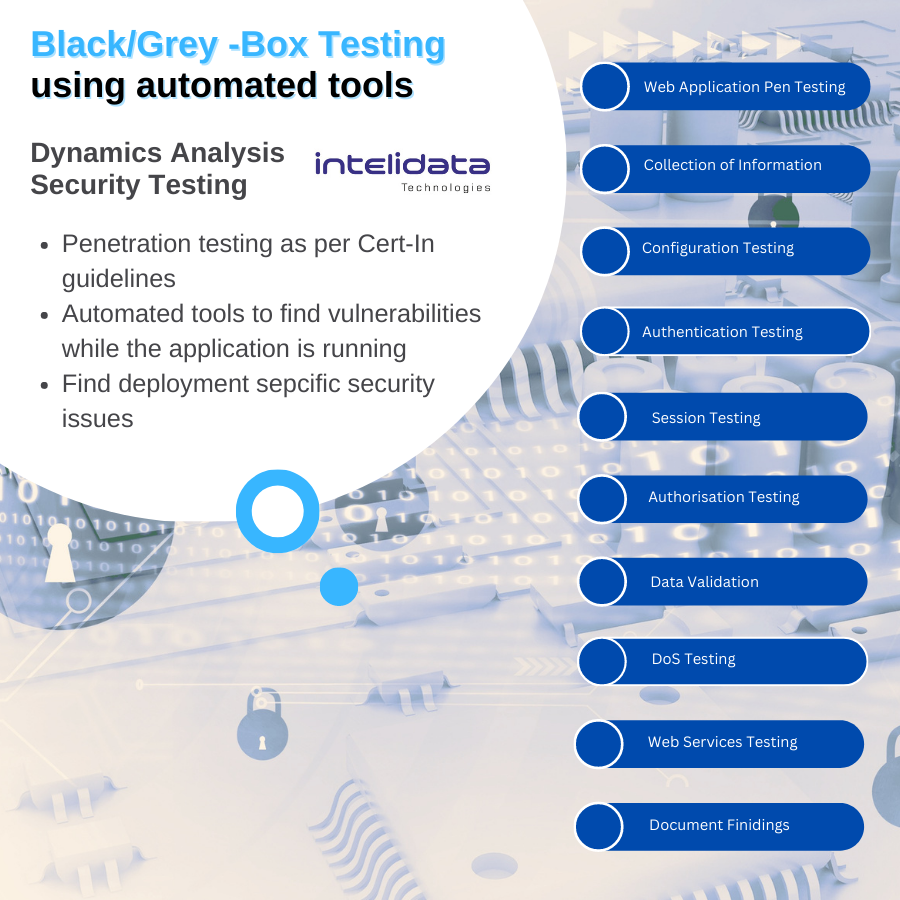
Why DAST?
•Black/Grey-box security testing using automated tools; examines an application as it’s running to find vulnerabilities that an attacker could exploit.
•SAST may not get full picture without application deployment
•DAST will help in picking out deployment specific issues
•Results from DAST and SAST can be compared to weed out false positives









Description
Technical Experience
We are a qualified & highly technical team of Experienced Cyber Security Researchers, with cumulative experience of 25+ years. We partner with small to mid-sized companies to secure their businesses with easy step-by-step proven processes & Cert-in guidelines.
24/7 Services
We offer round-the-clock technical assistance. We never turn the cell phone off. It’s on 24/7 and it gets answered whenever you call, to give you timely deliveries. By outsourcing your IT security to us, you can focus on what you do best–running your business.
Flexible Pricing
No unexpected bills. No budget blow-outs. No missed deadlines. No broken promises. No shoddy service. No surprises. We believe in adding value to your business and provide meaningful service at a very cost efficient and budget -friendly pricing.
Training Assistance
We provide detailed steps & Cyber Security training to your Web Administrators and Developers for patching. No matter the budget, we pride ourselves on providing comprehensive professional assistance to them to secure your business.