Description
INTRODUCTION
Thick client pentesting involves both local and server-side processing and often uses proprietary protocols for communication.
Simple automated assessment scanning is not sufficient and testing thick client applications requires a lot of patience and a methodical approach. Moreover, the process often requires specialized tools and custom testing setup.
ARCHITECTURE OF THICK CLIENT
Two-Tier Architecture
In two-tier architecture, the thick client application implements client-to-server communication. The application is installed on the client computer and, in order to work, will need to communicate with a database server. For example, imagine an HR application that was installed on the client computer and, in order to retrieve the employees’ information, communicates directly with the HR database server.
Three-Tier Architecture
In three-tier architecture, the client communicates with an application server, which in turn talks to the database in a manner similar to a regular web application. The most common communication method in these applications may be carried out using HTTP/HTTPS.
Three-tier architecture has a security advantage over two-tier architecture, because it prevents the end-user from communicating directly with the database server
METHODOLOGY






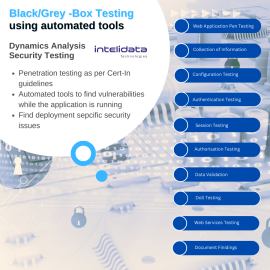


Description
Intect is top penetration testing and security assessment firm with a focus on web, mobile apps, network, and cloud testing. As a security partner, we identify and demonstrate the risk and the vulnerabilities which put clients at risk.
Our mission is to help our clients to secure their digital assets. We operate across India and in several other countries for clients who require our specialised skill sets.
Our team includes active security researchers, ethical hackers, bug bounty players & tool developers who are highly credentialed in their field. We work hard to stay at the forefront of cybersecurity industry and that is shown through our research and training.
Our penetration testing assessments are not just for a tick in the checkbox on the list of security requirements. The detailed reports we provide enable you to substantiate the security of your applications and networks to your stake-holders. Intect provides the technical expertise and guidance to find the gaps in your security.
Our consultants have expertise across a range of industries, including BFSI, e-Commerce, telecom, technology, enterprise suites, manufacturing, education and public sector.