Product categories
- Application Security
- Automotive Cyber Security
- Cloud Access Security Broker
- Cloud Security
- Cyber Security Services
- Data Security
- Endpoint Security
- Forensics
- Governance Risk Management & Compliance
- Infrastructure Security
- Mobile Security
- Network Security
- Password Manager
- Patch Configuration and Management
- Secure File Transfer
- Secure Web Gateway
- Security Information and Event Management
- Security Training Software
- Unified Threat Management
- User Security
- VAPT
-
Accops HySecure: ZTNA-based Application Access Gateway
ZTNA-based Access Gateway to reduce attack surface even in a perimeter-less hybrid work environment.Accops HySecure: ZTNA-based Application Access Gateway
ZTNA-based Access Gateway to reduce attack surface even in a perimeter-less hybrid work environment. -
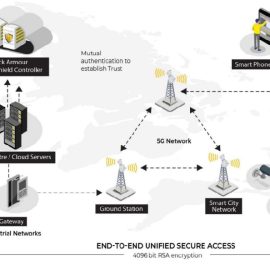
Block Armour Secure Shield
Block Armour Secure Shield is a Unified Secure Network Access Solution built on Zero Trust powered by SDP and Block Chain that protects Enterprise, Cloud and IOT Network Access scenarios for employees, third-party users and IOT devices and sensors as well. It can be used to ensure a secure WFH/BYOD experience and reduces the attack surface for malware and ransomware.Block Armour Secure Shield
Block Armour Secure Shield is a Unified Secure Network Access Solution built on Zero Trust powered by SDP and Block Chain that protects Enterprise, Cloud and IOT Network Access scenarios for employees, third-party users and IOT devices and sensors as well. It can be used to ensure a secure WFH/BYOD experience and reduces the attack surface for malware and ransomware. -
Calico Cloud
$36.50Calico Cloud is the industry’s only active Cloud-Native Application Protection Platform (CNAPP) with full-stack observability. It enables organizations to prevent attacks using zero trust, and to detect, troubleshoot, and automatically mitigate vulnerabilities and security threats in build, deploy, and runtime stages across multi-cloud and hybrid deployments. Calico Cloud supports multiple dataplanes including eBPF, Windows and Linux. With Calico Cloud, users get a fully managed pay-as-you-go SaaS platform for active build and runtime security of cloud-native applications running on containers and Kubernetes.Calico Cloud
Calico Cloud is the industry’s only active Cloud-Native Application Protection Platform (CNAPP) with full-stack observability. It enables organizations to prevent attacks using zero trust, and to detect, troubleshoot, and automatically mitigate vulnerabilities and security threats in build, deploy, and runtime stages across multi-cloud and hybrid deployments. Calico Cloud supports multiple dataplanes including eBPF, Windows and Linux. With Calico Cloud, users get a fully managed pay-as-you-go SaaS platform for active build and runtime security of cloud-native applications running on containers and Kubernetes. -
IoT Armour
With IoT Armour an organization can now move confidently into the journey of adopting IoT Sensors and Devices as part of their business processes. The solution utilizes a unique blockchain based digital identity for secure IOT device authentication and a policy based authorization to ensure only genuine devices and traffic is allowed to communicate with the IT based management systems. While reducing the attack surface available for attack by malware and ransomware.IoT Armour
With IoT Armour an organization can now move confidently into the journey of adopting IoT Sensors and Devices as part of their business processes. The solution utilizes a unique blockchain based digital identity for secure IOT device authentication and a policy based authorization to ensure only genuine devices and traffic is allowed to communicate with the IT based management systems. While reducing the attack surface available for attack by malware and ransomware. -
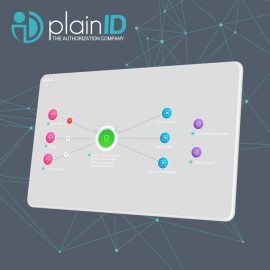
PlainID Policy Manager
PlainID’s Policy Manager gives you centralized management in a decentralized enforcement architecture. You get a focused view along with the ability to control who has access to what, across your digital landscape. It also provides improved visibility of access risks through advanced access control analytics. This allows a company to have predictive and prescriptive access controls, as well as run-time authorization enforcement using Policy-Based Access Control (PBAC) capabilities with workflows and SOD controls. It integrates with leading vendors in the IAM space such as SailPoint, Okta and Azure AD.
PlainID Policy Manager
PlainID’s Policy Manager gives you centralized management in a decentralized enforcement architecture. You get a focused view along with the ability to control who has access to what, across your digital landscape. It also provides improved visibility of access risks through advanced access control analytics. This allows a company to have predictive and prescriptive access controls, as well as run-time authorization enforcement using Policy-Based Access Control (PBAC) capabilities with workflows and SOD controls. It integrates with leading vendors in the IAM space such as SailPoint, Okta and Azure AD.
-
T2 COMMUNICATOR
$999.00T2 COMMUNICATOR secures mobile communication and data-at-rest. Engineered for organizations operating in the critical sectors. T2 COMMUNICATOR covers all critical vectors of attack:- hardware
- OS
- applications
- connectivity
T2 COMMUNICATOR
Category: Data-at-Rest Encryption Data-in-Motion Encryption Endpoint Security Messaging Security Mobile Communication Security Mobile Data Protection Mobile Device Management Secure File Transfer Zero trust |T2 COMMUNICATOR secures mobile communication and data-at-rest. Engineered for organizations operating in the critical sectors. T2 COMMUNICATOR covers all critical vectors of attack:- hardware
- OS
- applications
- connectivity
-
T2 COMMUNICATOR Dual OS
T2 COMMUNICATOR Dual is a unique Dual OS secure device for Professional and Professional use, eliminating the need of carrying multiple phones. It facilitates:
- Two completely separated and hardened operating systems
- Encrypted communication
- Secure file share and storage
- Malware, zero-click spyware, tracking, and IMSI-catcher protection
- Complete management of device permissions and policies
- An optional feature of self-hosting for unmatched security
T2 COMMUNICATOR and T2 COMMUNICATOR Dual
are engineered and trusted by organizations operating in critical sectors.
T2 COMMUNICATOR Dual OS
T2 COMMUNICATOR Dual is a unique Dual OS secure device for Professional and Professional use, eliminating the need of carrying multiple phones. It facilitates:
- Two completely separated and hardened operating systems
- Encrypted communication
- Secure file share and storage
- Malware, zero-click spyware, tracking, and IMSI-catcher protection
- Complete management of device permissions and policies
- An optional feature of self-hosting for unmatched security
T2 COMMUNICATOR and T2 COMMUNICATOR Dual
are engineered and trusted by organizations operating in critical sectors.
-
Zero Trust Isolation Platform
Zero Trust Isolation platform designed to contain, profile and stop lateral threat movement across any organization.Airgap ring fences every endpoint in a network of “1” to protect against lateral threat movement. AI/ML based technology continuously monitors devices and flows for anomaly detection and threat prevention.Zero Trust Isolation Platform
Zero Trust Isolation platform designed to contain, profile and stop lateral threat movement across any organization.Airgap ring fences every endpoint in a network of “1” to protect against lateral threat movement. AI/ML based technology continuously monitors devices and flows for anomaly detection and threat prevention.