Onefede > Products
Product categories
- Application Security
- Automotive Cyber Security
- Cloud Access Security Broker
- Cloud Security
- Cyber Security Services
- Data Security
- Endpoint Security
- Forensics
- Governance Risk Management & Compliance
- Infrastructure Security
- Mobile Security
- Network Security
- Password Manager
- Patch Configuration and Management
- Secure File Transfer
- Secure Web Gateway
- Security Information and Event Management
- Security Training Software
- Unified Threat Management
- User Security
- VAPT
-
Suite – Enterprise Tier
$1,999.00 / month with a 7-day free trialYou can now automate your red team task. Choose and schedule recurring attack simulations such as Phishing, External/Internal scans, domain scans, Vulnerability Assessments, and more! This includes PDF reports based on your findings with premium support and consultation. Own Your Pentesting: With the Enterprise Suite, CTOs and IT Security Professionals can finally move beyond manual pentesting and get intelligent, automated results. Twice as fast as a pentest and 5x cheaper. You can easily manage, schedule, and review pentests from a single dashboard.Suite – Enterprise Tier
You can now automate your red team task. Choose and schedule recurring attack simulations such as Phishing, External/Internal scans, domain scans, Vulnerability Assessments, and more! This includes PDF reports based on your findings with premium support and consultation. Own Your Pentesting: With the Enterprise Suite, CTOs and IT Security Professionals can finally move beyond manual pentesting and get intelligent, automated results. Twice as fast as a pentest and 5x cheaper. You can easily manage, schedule, and review pentests from a single dashboard.$1 999.00 -
Suite – Premium Tier
$100.00 / monthThis includes 100 Credits delivered monthly to your account! You can schedule what you want, when you need it, at the price you want it. You can now Schedule recurring simulations tests such as Phishing, external scans, domain scans, and more! This includes PDF reports based on your findings with premium support and consultation. Modules cost credits, Modules Included: ● Web Applications: HTTP(S), Source Code, Containerization, ● APIs: SOAP, REST, GraphQL ● Networks: Layers 1-7, Active Directory, LDAP, IPv6, Wireless ● OSINT: Leaked Users, Files ● Amazon Web Services ● Google Cloud Platform ● Microsoft Azure ● Kubernetes: App to Pod, Pod to Worker, Worker to Master, and so on ● Mobile & IoT Applications ● Social Engineering: Phishing, SMSSuite – Premium Tier
This includes 100 Credits delivered monthly to your account! You can schedule what you want, when you need it, at the price you want it. You can now Schedule recurring simulations tests such as Phishing, external scans, domain scans, and more! This includes PDF reports based on your findings with premium support and consultation. Modules cost credits, Modules Included: ● Web Applications: HTTP(S), Source Code, Containerization, ● APIs: SOAP, REST, GraphQL ● Networks: Layers 1-7, Active Directory, LDAP, IPv6, Wireless ● OSINT: Leaked Users, Files ● Amazon Web Services ● Google Cloud Platform ● Microsoft Azure ● Kubernetes: App to Pod, Pod to Worker, Worker to Master, and so on ● Mobile & IoT Applications ● Social Engineering: Phishing, SMS -
Suite – Starter Tier
Pay as you go! Create an account and get a vulnerability scan today! -Consultation and PDF Reporting - Schedule any scans: ● Web Applications: HTTP(S), Source Code, Containerization, ● APIs: SOAP, REST, GraphQL ● Networks: Layers 1-7, Active ●Directory, LDAP, IPv6, Wireless ● OSINT: Leaked Users, Files ● Amazon Web Services ● Google Cloud Platform ● Microsoft Azure ● Kubernetes: App to Pod, Pod to Worker, Worker to Master, and so on ● Mobile & IoT Applications ● Social Engineering: Phishing, SMSSuite – Starter Tier
Pay as you go! Create an account and get a vulnerability scan today! -Consultation and PDF Reporting - Schedule any scans: ● Web Applications: HTTP(S), Source Code, Containerization, ● APIs: SOAP, REST, GraphQL ● Networks: Layers 1-7, Active ●Directory, LDAP, IPv6, Wireless ● OSINT: Leaked Users, Files ● Amazon Web Services ● Google Cloud Platform ● Microsoft Azure ● Kubernetes: App to Pod, Pod to Worker, Worker to Master, and so on ● Mobile & IoT Applications ● Social Engineering: Phishing, SMS -
T2 COMMUNICATOR
$999.00T2 COMMUNICATOR secures mobile communication and data-at-rest. Engineered for organizations operating in the critical sectors. T2 COMMUNICATOR covers all critical vectors of attack:- hardware
- OS
- applications
- connectivity
T2 COMMUNICATOR
Category: Data-at-Rest Encryption Data-in-Motion Encryption Endpoint Security Messaging Security Mobile Communication Security Mobile Data Protection Mobile Device Management Secure File Transfer Zero trust |T2 COMMUNICATOR secures mobile communication and data-at-rest. Engineered for organizations operating in the critical sectors. T2 COMMUNICATOR covers all critical vectors of attack:- hardware
- OS
- applications
- connectivity
-
T2 COMMUNICATOR Dual OS
T2 COMMUNICATOR Dual is a unique Dual OS secure device for Professional and Professional use, eliminating the need of carrying multiple phones. It facilitates:
- Two completely separated and hardened operating systems
- Encrypted communication
- Secure file share and storage
- Malware, zero-click spyware, tracking, and IMSI-catcher protection
- Complete management of device permissions and policies
- An optional feature of self-hosting for unmatched security
T2 COMMUNICATOR and T2 COMMUNICATOR Dual
are engineered and trusted by organizations operating in critical sectors.
T2 COMMUNICATOR Dual OS
T2 COMMUNICATOR Dual is a unique Dual OS secure device for Professional and Professional use, eliminating the need of carrying multiple phones. It facilitates:
- Two completely separated and hardened operating systems
- Encrypted communication
- Secure file share and storage
- Malware, zero-click spyware, tracking, and IMSI-catcher protection
- Complete management of device permissions and policies
- An optional feature of self-hosting for unmatched security
T2 COMMUNICATOR and T2 COMMUNICATOR Dual
are engineered and trusted by organizations operating in critical sectors.
-
TDMARC – ThreatCop DMARC
TDMARC is an anti-spoofing and email authentication solution that helps organizations secure their outbound email flow and prevent the misuse of their email domain while boosting email deliverability and engagement rates.TDMARC – ThreatCop DMARC
TDMARC is an anti-spoofing and email authentication solution that helps organizations secure their outbound email flow and prevent the misuse of their email domain while boosting email deliverability and engagement rates. -
Thick Client VAPT
$110.00Thick client applications are generally more complicated and customized than web or mobile applications, so they need a specific approach when it comes to a penetration test. Our team discovers what technology is being used at client and server end, figures out application functionality and behavior, identify all entry points for user input, understand the core security mechanisms, and then proceed to find vulnerabilities.Thick Client VAPT
Thick client applications are generally more complicated and customized than web or mobile applications, so they need a specific approach when it comes to a penetration test. Our team discovers what technology is being used at client and server end, figures out application functionality and behavior, identify all entry points for user input, understand the core security mechanisms, and then proceed to find vulnerabilities. -
Threat Hunting Services by SecurDefense
$7,500.00Cyber Attacks have become sophisticated than ever before. Organizations are challenged with proactively detecting the attacks, respond and timely mitigation. Typically Organizations deploy Security platforms like firewalls, Intrusion Detection / Preventions etc. However, attackers use new techniques and hide the attack below normal protocol and operations. Not only that, they dynamically keep changing the attack landscape and attack delivery methods. In this advance Technical exercise, we will use Threat intelligence and SIEM (Security Information and Event Management technologies to detect variety of threats.Threat Hunting Services by SecurDefense
Cyber Attacks have become sophisticated than ever before. Organizations are challenged with proactively detecting the attacks, respond and timely mitigation. Typically Organizations deploy Security platforms like firewalls, Intrusion Detection / Preventions etc. However, attackers use new techniques and hide the attack below normal protocol and operations. Not only that, they dynamically keep changing the attack landscape and attack delivery methods. In this advance Technical exercise, we will use Threat intelligence and SIEM (Security Information and Event Management technologies to detect variety of threats. -
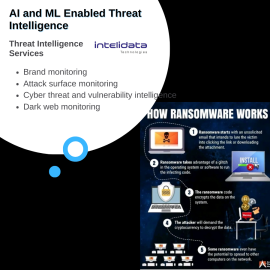
Threat Intelligence Services by Intelidata
Intelidata provides advanced threat intelligence with 360 degree coverage. The coverage includes:- Brand monitoring
- Social media monitoring
- Attack surface monitoring
- Cyber threat and vulnerability intelligence
- Cyber crime and dark web monitoring
- Supplier risk monitoring
Threat Intelligence Services by Intelidata
Intelidata provides advanced threat intelligence with 360 degree coverage. The coverage includes:- Brand monitoring
- Social media monitoring
- Attack surface monitoring
- Cyber threat and vulnerability intelligence
- Cyber crime and dark web monitoring
- Supplier risk monitoring
-
TPIR – ThreatCop Phishing Incident Response
TPIR is an email threat checker and a phishing incident response solution that empowers your employees to proactively detect and report suspicious emails, reducing the risk of email-based cyber threats.TPIR – ThreatCop Phishing Incident Response
TPIR is an email threat checker and a phishing incident response solution that empowers your employees to proactively detect and report suspicious emails, reducing the risk of email-based cyber threats. -
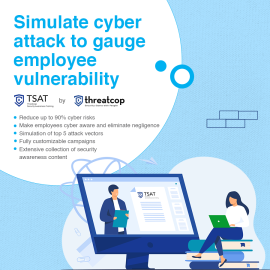
TSAT- ThreatCop Security Awareness Training
TSAT is a cyber attack simulator and a security awareness training solution that allows you to run dummy cyber attack campaigns on your employees to assess their vulnerability levels. It helps you generate security awareness amongst your people to reduce the risk of cyber attacks.TSAT- ThreatCop Security Awareness Training
TSAT is a cyber attack simulator and a security awareness training solution that allows you to run dummy cyber attack campaigns on your employees to assess their vulnerability levels. It helps you generate security awareness amongst your people to reduce the risk of cyber attacks. -
User Behaviour Analytics
End users, not the machines, pose the biggest security challenge in the fast-changing IT infrastructure landscape. While compromise of privileged credentials remains one of the most feared IT threats of an enterprise IT security team, more and more IT incidents are stemming from anomalous end user behavioral profiles. Threat Detection and real-time analytics is a need of the hour.
ARCON | User Behaviour Analytics solution offer enterprise IT security teams with necessary tools to crunch a large lake of enterprise data, spot anomalous and risky behavior profiles along with a capability to trigger alerts in real-time.User Behaviour Analytics
End users, not the machines, pose the biggest security challenge in the fast-changing IT infrastructure landscape. While compromise of privileged credentials remains one of the most feared IT threats of an enterprise IT security team, more and more IT incidents are stemming from anomalous end user behavioral profiles. Threat Detection and real-time analytics is a need of the hour.
ARCON | User Behaviour Analytics solution offer enterprise IT security teams with necessary tools to crunch a large lake of enterprise data, spot anomalous and risky behavior profiles along with a capability to trigger alerts in real-time. -
Valydate4U – A digital Onboarding Platform
Valydate4u Is a Complete 100% Paperless, Secure, KYC, VKYC, and Digital On-Boarding platform. Consent-Based, 100% Secured, Faceless, Fast (reduces time from 30mins To 2 Mins) Agent Or Self On-Boarding. Compliant With India’s RBI, Malaysia EKYC, And Other Global Standards.Valydate4U – A digital Onboarding Platform
Category: Fraud Prevention Identity and Access Management Identity Theft Detection User Authentication |Valydate4u Is a Complete 100% Paperless, Secure, KYC, VKYC, and Digital On-Boarding platform. Consent-Based, 100% Secured, Faceless, Fast (reduces time from 30mins To 2 Mins) Agent Or Self On-Boarding. Compliant With India’s RBI, Malaysia EKYC, And Other Global Standards. -
VAPT by SecurDefense
$29.00A powerful testing practice targeted to analyze how breaches could enable unauthorized access to resources be they the systems, data, network or the applications has to be Penetration Testing Focused to provide security across the extended networks, Penetration tests keep a check on security measures right from the On Premise Enterprise Systems to the Enterprise Mobility solutions and their devices and networks, various websites and web based solutions, right up to the Cloud.VAPT by SecurDefense
A powerful testing practice targeted to analyze how breaches could enable unauthorized access to resources be they the systems, data, network or the applications has to be Penetration Testing Focused to provide security across the extended networks, Penetration tests keep a check on security measures right from the On Premise Enterprise Systems to the Enterprise Mobility solutions and their devices and networks, various websites and web based solutions, right up to the Cloud. -
Virtual CISO as a Service by Intelidata
A V-CISO is your security point-of-contact for all security related issues, offering a direct line to experts as questions naturally arise. A virtual CISO will also respond to incidents, answer security-related questionnaires for your customers, and respond to data breach should that arise. In addition to ongoing and ad hoc support, a v CISO will tie into meetings when security expertise and guidance are needed. With our Cyber Security Consulting, we offer a no-compromise solution that eliminates new hire commitments while delivering the executive-level counsel needed to succeed. We’ll work alongside your management to best align security policies and practices with business objectives to advance your operational goals.Virtual CISO as a Service by Intelidata
A V-CISO is your security point-of-contact for all security related issues, offering a direct line to experts as questions naturally arise. A virtual CISO will also respond to incidents, answer security-related questionnaires for your customers, and respond to data breach should that arise. In addition to ongoing and ad hoc support, a v CISO will tie into meetings when security expertise and guidance are needed. With our Cyber Security Consulting, we offer a no-compromise solution that eliminates new hire commitments while delivering the executive-level counsel needed to succeed. We’ll work alongside your management to best align security policies and practices with business objectives to advance your operational goals. -
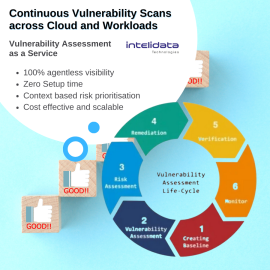
Vulnerability Assessment as a Service by Intelidata
Vulnerability Assessment Tool: Continuous vulnerability scan across clouds and workloads. Context-based prioritization based on exposure and impact. It can cover: Web App Security: Detect, patch security gaps in static websites, complex web apps and APIs Mobile App Security: Automated advanced security assessment of mobile applications - Android, iOS, WindowsVulnerability Assessment as a Service by Intelidata
Vulnerability Assessment Tool: Continuous vulnerability scan across clouds and workloads. Context-based prioritization based on exposure and impact. It can cover: Web App Security: Detect, patch security gaps in static websites, complex web apps and APIs Mobile App Security: Automated advanced security assessment of mobile applications - Android, iOS, Windows