Product categories
- Application Security
- Automotive Cyber Security
- Cloud Access Security Broker
- Cloud Security
- Cyber Security Services
- Data Security
- Endpoint Security
- Forensics
- Governance Risk Management & Compliance
- Infrastructure Security
- Mobile Security
- Network Security
- Password Manager
- Patch Configuration and Management
- Secure File Transfer
- Secure Web Gateway
- Security Information and Event Management
- Security Training Software
- Unified Threat Management
- User Security
- VAPT
-
SecurDPS Discover and Classify
Comforte’s Discovery and Classification solution is a unique and proprietary passive network packet capture process to identify sensitive data (such as highly-regulated PII) flowing through the organization. This flow visibility enables our solution to identify repositories (databases, applications, file systems, and log files) where sensitive data resides. The solution then does a comprehensive scan of those repositories to get full visibility into the depth and breadth of the data environment. Finally, it analyzes and consolidates the data identified as a result of those scans in a structure that allows the user to see data lineage, respond to subject access requests, identify production data in non-production locations, and many other privacy, security, and data governance tasks.SecurDPS Discover and Classify
Comforte’s Discovery and Classification solution is a unique and proprietary passive network packet capture process to identify sensitive data (such as highly-regulated PII) flowing through the organization. This flow visibility enables our solution to identify repositories (databases, applications, file systems, and log files) where sensitive data resides. The solution then does a comprehensive scan of those repositories to get full visibility into the depth and breadth of the data environment. Finally, it analyzes and consolidates the data identified as a result of those scans in a structure that allows the user to see data lineage, respond to subject access requests, identify production data in non-production locations, and many other privacy, security, and data governance tasks. -
SecurDPS Enterprise
SecurDPS Enterprise allows organizations to take complete control of their sensitive data. Protecting sensitive data with a data-centric security approach helps your organization to comply with privacy regulations, reduce the risk of breaches and monetize valuable data – while improving your competitive advantage. Today SecurDPS Enterprise is protecting hundreds of millions of payment transactions, healthcare records, insurance records, and more, reliably running in business-critical environments.SecurDPS Enterprise
SecurDPS Enterprise allows organizations to take complete control of their sensitive data. Protecting sensitive data with a data-centric security approach helps your organization to comply with privacy regulations, reduce the risk of breaches and monetize valuable data – while improving your competitive advantage. Today SecurDPS Enterprise is protecting hundreds of millions of payment transactions, healthcare records, insurance records, and more, reliably running in business-critical environments. -
Secure Code Review
$100.00Secure Code reviews are an effective method for finding bugs that can be difficult or impossible to find during black box or grey box testing. Our team utilizes best-in-class code review tools to scan the full codebase followed by a deep manual examination for areas of critical importance.Secure Code Review
Secure Code reviews are an effective method for finding bugs that can be difficult or impossible to find during black box or grey box testing. Our team utilizes best-in-class code review tools to scan the full codebase followed by a deep manual examination for areas of critical importance. -
Secure Communication by KoolSpan Dome
Mobile Secure Communicatoin Solution: exclusive military-grade end-to-end encryption and security for voice calls, messaging and file sharing. Designed to operate on-prem in fully enclosed network environmentsSecure Communication by KoolSpan Dome
Mobile Secure Communicatoin Solution: exclusive military-grade end-to-end encryption and security for voice calls, messaging and file sharing. Designed to operate on-prem in fully enclosed network environments -
SecureTower
SecureTower is a 2 in 1 Solution: Data Leak Protection + Employee Monitoring. It's key features include: - Data leak protection - Staff efficiency and loyalty monitoring - Identification of potentially dangerous employees (risk analysis) - Business communications archive maintainingSecureTower
Category: Data Breach Protection Data Leakage Prevention Data Security File Content Security Secure File Transfer | SKU: STSecureTower is a 2 in 1 Solution: Data Leak Protection + Employee Monitoring. It's key features include: - Data leak protection - Staff efficiency and loyalty monitoring - Identification of potentially dangerous employees (risk analysis) - Business communications archive maintaining -
Security Compliance Management
ARCON | Security Compliance Management (SCM) is a highly effective enterprise-grade solution to identify, assess and mitigate system vulnerabilities. ARCON|SCM automates the entire risk assessment process, manages execution and generates detailed review documentation of IT risk factors. The vulnerability assessment solution enhances IT controls and visibility by setting-up baseline security configurations and policies for disparate technology platforms. Enterprise IT risk management teams find ARCON| SCM as a robust technology to adhere to various IT security standards for compliance purposes as well.Security Compliance Management
ARCON | Security Compliance Management (SCM) is a highly effective enterprise-grade solution to identify, assess and mitigate system vulnerabilities. ARCON|SCM automates the entire risk assessment process, manages execution and generates detailed review documentation of IT risk factors. The vulnerability assessment solution enhances IT controls and visibility by setting-up baseline security configurations and policies for disparate technology platforms. Enterprise IT risk management teams find ARCON| SCM as a robust technology to adhere to various IT security standards for compliance purposes as well. -
Security Service Edge by Netskope
Netskope Intelligent Security Service Edge is fast, easy to use, and secures your transactions wherever your people and data go. Netskope SSE converges security capabilities into a single cloud platform. Netskope helps you reduce risk, accelerate performance, and provide unrivaled visibility into any cloud, web, and private application activity. To empower safe collaboration, we balance trust against risk with granular controls that adapt to changes in your environment. Netskope SSE protects against advanced and cloud-enabled threats and safeguards data across all vectors (any cloud, any app, any user). A single-pass architecture delivers a fast user experience and simplified operations.Security Service Edge by Netskope
Netskope Intelligent Security Service Edge is fast, easy to use, and secures your transactions wherever your people and data go. Netskope SSE converges security capabilities into a single cloud platform. Netskope helps you reduce risk, accelerate performance, and provide unrivaled visibility into any cloud, web, and private application activity. To empower safe collaboration, we balance trust against risk with granular controls that adapt to changes in your environment. Netskope SSE protects against advanced and cloud-enabled threats and safeguards data across all vectors (any cloud, any app, any user). A single-pass architecture delivers a fast user experience and simplified operations. -
SentinelOne Singularity XDR Platform
SentinelOne Singularity XDR unifies and extends detection, investigation and response capability across the entire enterprise, providing security teams with centralized end-to-end enterprise visibility, powerful analytics, and automatable response across the technology stack. The solution empowers security teams to see data collected by disparate security solutions from all platforms, including endpoints, cloud workloads, network devices, email, identity, and more, within a single dashboard. The solution delivers increased flexibility, automation and simplicity with unparalleled scale to every environment based on an industry leading foundation of EPP & EDR.SentinelOne Singularity XDR Platform
SentinelOne Singularity XDR unifies and extends detection, investigation and response capability across the entire enterprise, providing security teams with centralized end-to-end enterprise visibility, powerful analytics, and automatable response across the technology stack. The solution empowers security teams to see data collected by disparate security solutions from all platforms, including endpoints, cloud workloads, network devices, email, identity, and more, within a single dashboard. The solution delivers increased flexibility, automation and simplicity with unparalleled scale to every environment based on an industry leading foundation of EPP & EDR. -
SOC as a Service by Intelidata
Intelidata Managed Services powered with SOC tools believes in taking a holistic approach to cyber security by gathering deep insights from endpoints, servers, network devices, applications, IOT and security systems and applying user identity, threat intelligence and vulnerability assessment to establish threat profile, generate threat indicators, raise essential alerts and offer remediation path – automated or triaged. In essence, the solution ensures multi-layered threat detection and response, relying on EDR, Network Behavior, Advanced Correlation (SIEM), Network Traffic Analysis, UEBA (ML based) and SOAR for an All-In-One experience that is organically and seamlessly fused together. It empowers SOC analysts to become more efficient and helps organizations to reduce MTTI and MTTR together providing continuous compliance for the business.SOC as a Service by Intelidata
Intelidata Managed Services powered with SOC tools believes in taking a holistic approach to cyber security by gathering deep insights from endpoints, servers, network devices, applications, IOT and security systems and applying user identity, threat intelligence and vulnerability assessment to establish threat profile, generate threat indicators, raise essential alerts and offer remediation path – automated or triaged. In essence, the solution ensures multi-layered threat detection and response, relying on EDR, Network Behavior, Advanced Correlation (SIEM), Network Traffic Analysis, UEBA (ML based) and SOAR for an All-In-One experience that is organically and seamlessly fused together. It empowers SOC analysts to become more efficient and helps organizations to reduce MTTI and MTTR together providing continuous compliance for the business. -
SOC2 Audit Services by Riskpro
Riskpro's unique approach to SOC2 audit engagement is sustained value addition to your business. Our readiness services enable you to remediate the control gaps in an efficient manner that not only help to get SOC 2 reports signed, but also improve productivity and efficiency in the business.SOC2 Audit Services by Riskpro
Riskpro's unique approach to SOC2 audit engagement is sustained value addition to your business. Our readiness services enable you to remediate the control gaps in an efficient manner that not only help to get SOC 2 reports signed, but also improve productivity and efficiency in the business. -
Social engineering / Employee Vulnerability Assessment
$100.00Through social engineering assessments, we’ll demonstrate how well employees are complying with organizational procedures and processes.Social engineering / Employee Vulnerability Assessment
Through social engineering assessments, we’ll demonstrate how well employees are complying with organizational procedures and processes. -
SOCRadar Cyber Intelligence
SOCRadar provides actionable and contextualized intelligence aiming for security teams to operate efficiently. Our platform’s end-to-end automation supports SOC teams in dealing with manual and repetitive tasks that simultaneously minimize zero positives so that security analysts should focus on higher-impact projects. With SOCRadar’s early-warning system that detects attacks in the pre-exploit period, getting ahead of cyber attackers is now possible. Challenged by the understaffed teams, security leaders can effectively use SOCRadar as an extension to SOC teams.SOCRadar Cyber Intelligence
SOCRadar provides actionable and contextualized intelligence aiming for security teams to operate efficiently. Our platform’s end-to-end automation supports SOC teams in dealing with manual and repetitive tasks that simultaneously minimize zero positives so that security analysts should focus on higher-impact projects. With SOCRadar’s early-warning system that detects attacks in the pre-exploit period, getting ahead of cyber attackers is now possible. Challenged by the understaffed teams, security leaders can effectively use SOCRadar as an extension to SOC teams. -
Software Compliance Audit & Management by SecurDefense
$3,000.00Our passion is to give our customers the absolutely correct view of all their software Products Deployments. Microsoft, Autodesk, Adobe, Oracle products from 136 global software publishers are tracked by our application. . We will install Euladox Auditor on premise & train you on conducting discovery across the network. Conduct Discovery across your network domains & on systems not connected to the network. We will analyze data, run the software recognition engine and map the discovered programs to deployed licenses. We provide a deployment & compliance report for all products installed across your enterprise.Software Compliance Audit & Management by SecurDefense
Our passion is to give our customers the absolutely correct view of all their software Products Deployments. Microsoft, Autodesk, Adobe, Oracle products from 136 global software publishers are tracked by our application. . We will install Euladox Auditor on premise & train you on conducting discovery across the network. Conduct Discovery across your network domains & on systems not connected to the network. We will analyze data, run the software recognition engine and map the discovered programs to deployed licenses. We provide a deployment & compliance report for all products installed across your enterprise. -
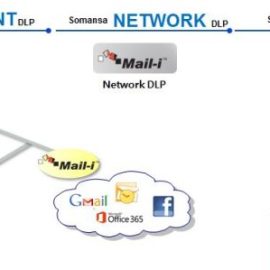
Somansa Data Leak Prevention
$70.00 – $120.00 / year• Data Discovery with classification • Data Leak Prevention • Encryption • Approval Management • Real time alerts and robust reporting
Protect Sensitive Data, Meet Regulatory Compliance Requirements.
Somansa is robust DLP, which can cater to all type of organizations & all requirements on DLP.
Endpoint Data Loss Prevention: Discover, Monitor, Prevent Sensitive Data Leakage on Your Endpoints
Network Data Loss Prevention: Secure Sensitive Data in Motion Before It Leaves Your Network
Somansa DLP: Prevent sensitive data in motion Emails, Cloud Services including Office 365 and Google G Suite and at rest, Removable Storage, Printing, Applications based on content, context aware policies.
Secure Data in Motion, Data at Rest, Encryption
Somansa Data Leak Prevention
Category: Data Discovery Data Leakage Prevention Data Security Digital Forensic Investigation and Computer Forensics | SKU: License• Data Discovery with classification • Data Leak Prevention • Encryption • Approval Management • Real time alerts and robust reporting
Protect Sensitive Data, Meet Regulatory Compliance Requirements.
Somansa is robust DLP, which can cater to all type of organizations & all requirements on DLP.
Endpoint Data Loss Prevention: Discover, Monitor, Prevent Sensitive Data Leakage on Your Endpoints
Network Data Loss Prevention: Secure Sensitive Data in Motion Before It Leaves Your Network
Somansa DLP: Prevent sensitive data in motion Emails, Cloud Services including Office 365 and Google G Suite and at rest, Removable Storage, Printing, Applications based on content, context aware policies.
Secure Data in Motion, Data at Rest, Encryption
$70.00 – $120.00 / year -
Standard Compliance
An organization's set of rules and regulations that are specialized to a given industry. In other terms, statutory compliance is the act of scrupulously upholding norms that businesses are compelled to adhere to. In order to protect customer data, the company must follow industry standards. Kratikal helps organizations get compliances for ISO27001, GDPR,HIPAA, SOC 1, SOC 2, and PCI DSSStandard Compliance
An organization's set of rules and regulations that are specialized to a given industry. In other terms, statutory compliance is the act of scrupulously upholding norms that businesses are compelled to adhere to. In order to protect customer data, the company must follow industry standards. Kratikal helps organizations get compliances for ISO27001, GDPR,HIPAA, SOC 1, SOC 2, and PCI DSS -
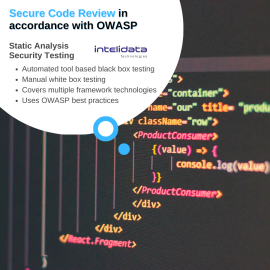
Static Analysis Security Testing by Intelidata
Static Analysis Security Testing (SAST) services by Intelidata to support developers in writing secure code and ensure application security. Secure Code Review is performed in accordance with Open Web Application Security Project (OWASP) industry best practice guidelines. At minimum, security assessment must include OWASP Top 10 security risk. Techniques to secure code review:- Automated tool based/ Black Box: In this approach, the secure code review is done using different open source/commercial tools.
- Manual/ White Box: The automatic tool scanner flags the whole code with vulnerabilities based on its perception. Thus a manual / white box testing is required.
Static Analysis Security Testing by Intelidata
Static Analysis Security Testing (SAST) services by Intelidata to support developers in writing secure code and ensure application security. Secure Code Review is performed in accordance with Open Web Application Security Project (OWASP) industry best practice guidelines. At minimum, security assessment must include OWASP Top 10 security risk. Techniques to secure code review:- Automated tool based/ Black Box: In this approach, the secure code review is done using different open source/commercial tools.
- Manual/ White Box: The automatic tool scanner flags the whole code with vulnerabilities based on its perception. Thus a manual / white box testing is required.