Product categories
- Application Security
- Automotive Cyber Security
- Cloud Access Security Broker
- Cloud Security
- Cyber Security Services
- Data Security
- Endpoint Security
- Forensics
- Governance Risk Management & Compliance
- Infrastructure Security
- Mobile Security
- Network Security
- Password Manager
- Patch Configuration and Management
- Secure File Transfer
- Secure Web Gateway
- Security Information and Event Management
- Security Training Software
- Unified Threat Management
- User Security
- VAPT
-
SCRUTINY SENSOR
Scrutiny predicts the true nature of files by emulating the static and dynamic behavior in a crypto caged environment and simultaneously training self-learning sensors at the same time to provide accurate verdicts along with detailed analysis in seconds. Our unique approach detects both known and unknown ransomware strains without any reliance on data engrams, centralized signature databases, etc. Also, this stands out as multi-tier, more innovative, and advanced than the other ransomware detection methods available.SCRUTINY SENSOR
Category: Cloud Security Data Security Email Security Endpoint Security Industrial Security Internet of Things Security Malware Detection and Analysis |Scrutiny predicts the true nature of files by emulating the static and dynamic behavior in a crypto caged environment and simultaneously training self-learning sensors at the same time to provide accurate verdicts along with detailed analysis in seconds. Our unique approach detects both known and unknown ransomware strains without any reliance on data engrams, centralized signature databases, etc. Also, this stands out as multi-tier, more innovative, and advanced than the other ransomware detection methods available. -
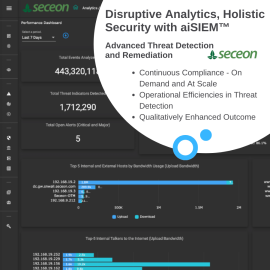
Seceon aiSIEM
Seceon's aiSIEM takes a radically different approach to cybersecurity, ensuring pitfalls of traditional SIEM are averted while empowering enterprises to take on the challenges posed by emerging threat vectors, techniques and tactics.
Protect all your digital assets, people and network round-the-clock at a fraction of the cost. Real time advanced threat detection and auto-remediation with Machine Learning and Artificial Intelligence.Stop the breach and keep business continuity at affordable cost! Catch and neutralize known and unknown threats across your digital assets – on-premise, cloud or remote – before they turn into major incidents.Seceon aiSIEM
Category: Malware Detection and Analysis Security Incident Management and Response Security Information and Event Management |Seceon's aiSIEM takes a radically different approach to cybersecurity, ensuring pitfalls of traditional SIEM are averted while empowering enterprises to take on the challenges posed by emerging threat vectors, techniques and tactics.
Protect all your digital assets, people and network round-the-clock at a fraction of the cost. Real time advanced threat detection and auto-remediation with Machine Learning and Artificial Intelligence.Stop the breach and keep business continuity at affordable cost! Catch and neutralize known and unknown threats across your digital assets – on-premise, cloud or remote – before they turn into major incidents. -
Seceon Open Threat Management Platform
Seceon’s Open Threat Management Platform makes the best out of available information and intelligence from various digital assets – guided by ML based behavioral analytics and AI based decision-making – to raise and eliminate only the qualified cyber security threats, proactively and confidently.By leveraging cutting edge technologies, the platform brings best-of-breed cyber threat detection techniques, visualization, remediation and reporting with 75%-90% reduction in Capex and Opex.
Seceon’s Open Threat Management Platform strikes a fine balance between automation, visibility, insights and custom controls. OTM optimizes analytics, reduces time-to-detection, time-to-remediation and provides control mechanisms to enforce network policies for micro-segmentation and custom user-defined-alerts.
Seceon Open Threat Management Platform
Seceon’s Open Threat Management Platform makes the best out of available information and intelligence from various digital assets – guided by ML based behavioral analytics and AI based decision-making – to raise and eliminate only the qualified cyber security threats, proactively and confidently.By leveraging cutting edge technologies, the platform brings best-of-breed cyber threat detection techniques, visualization, remediation and reporting with 75%-90% reduction in Capex and Opex.
Seceon’s Open Threat Management Platform strikes a fine balance between automation, visibility, insights and custom controls. OTM optimizes analytics, reduces time-to-detection, time-to-remediation and provides control mechanisms to enforce network policies for micro-segmentation and custom user-defined-alerts.
-
Securaa – Security Automation Platform
Securaa is a Comprehensive No Code Security Automation Platform that blends intelligence, risk-based asset management, vulnerability insights, automation and incident response into a single platform enabling SOC’s to reduce cybersecurity response time significantly and increase throughput manifolds.- Best RoI in the industry
- Reduce response time by over 95%
- Increase productivity by 300%
- Automate 100% L1 tasks
- Implement in weeks
- Build new playbook in hours
Securaa – Security Automation Platform
Securaa is a Comprehensive No Code Security Automation Platform that blends intelligence, risk-based asset management, vulnerability insights, automation and incident response into a single platform enabling SOC’s to reduce cybersecurity response time significantly and increase throughput manifolds.- Best RoI in the industry
- Reduce response time by over 95%
- Increase productivity by 300%
- Automate 100% L1 tasks
- Implement in weeks
- Build new playbook in hours
-
Social engineering / Employee Vulnerability Assessment
$100.00Through social engineering assessments, we’ll demonstrate how well employees are complying with organizational procedures and processes.Social engineering / Employee Vulnerability Assessment
Through social engineering assessments, we’ll demonstrate how well employees are complying with organizational procedures and processes. -
SOCRadar Cyber Intelligence
SOCRadar provides actionable and contextualized intelligence aiming for security teams to operate efficiently. Our platform’s end-to-end automation supports SOC teams in dealing with manual and repetitive tasks that simultaneously minimize zero positives so that security analysts should focus on higher-impact projects. With SOCRadar’s early-warning system that detects attacks in the pre-exploit period, getting ahead of cyber attackers is now possible. Challenged by the understaffed teams, security leaders can effectively use SOCRadar as an extension to SOC teams.SOCRadar Cyber Intelligence
SOCRadar provides actionable and contextualized intelligence aiming for security teams to operate efficiently. Our platform’s end-to-end automation supports SOC teams in dealing with manual and repetitive tasks that simultaneously minimize zero positives so that security analysts should focus on higher-impact projects. With SOCRadar’s early-warning system that detects attacks in the pre-exploit period, getting ahead of cyber attackers is now possible. Challenged by the understaffed teams, security leaders can effectively use SOCRadar as an extension to SOC teams. -
Threat Hunting Services by SecurDefense
$7,500.00Cyber Attacks have become sophisticated than ever before. Organizations are challenged with proactively detecting the attacks, respond and timely mitigation. Typically Organizations deploy Security platforms like firewalls, Intrusion Detection / Preventions etc. However, attackers use new techniques and hide the attack below normal protocol and operations. Not only that, they dynamically keep changing the attack landscape and attack delivery methods. In this advance Technical exercise, we will use Threat intelligence and SIEM (Security Information and Event Management technologies to detect variety of threats.Threat Hunting Services by SecurDefense
Cyber Attacks have become sophisticated than ever before. Organizations are challenged with proactively detecting the attacks, respond and timely mitigation. Typically Organizations deploy Security platforms like firewalls, Intrusion Detection / Preventions etc. However, attackers use new techniques and hide the attack below normal protocol and operations. Not only that, they dynamically keep changing the attack landscape and attack delivery methods. In this advance Technical exercise, we will use Threat intelligence and SIEM (Security Information and Event Management technologies to detect variety of threats. -
Threat Intelligence Services by Intelidata
Intelidata provides advanced threat intelligence with 360 degree coverage. The coverage includes:- Brand monitoring
- Social media monitoring
- Attack surface monitoring
- Cyber threat and vulnerability intelligence
- Cyber crime and dark web monitoring
- Supplier risk monitoring
Threat Intelligence Services by Intelidata
Intelidata provides advanced threat intelligence with 360 degree coverage. The coverage includes:- Brand monitoring
- Social media monitoring
- Attack surface monitoring
- Cyber threat and vulnerability intelligence
- Cyber crime and dark web monitoring
- Supplier risk monitoring
-
TPIR – ThreatCop Phishing Incident Response
TPIR is an email threat checker and a phishing incident response solution that empowers your employees to proactively detect and report suspicious emails, reducing the risk of email-based cyber threats.TPIR – ThreatCop Phishing Incident Response
TPIR is an email threat checker and a phishing incident response solution that empowers your employees to proactively detect and report suspicious emails, reducing the risk of email-based cyber threats. -
User Behaviour Analytics
End users, not the machines, pose the biggest security challenge in the fast-changing IT infrastructure landscape. While compromise of privileged credentials remains one of the most feared IT threats of an enterprise IT security team, more and more IT incidents are stemming from anomalous end user behavioral profiles. Threat Detection and real-time analytics is a need of the hour.
ARCON | User Behaviour Analytics solution offer enterprise IT security teams with necessary tools to crunch a large lake of enterprise data, spot anomalous and risky behavior profiles along with a capability to trigger alerts in real-time.User Behaviour Analytics
End users, not the machines, pose the biggest security challenge in the fast-changing IT infrastructure landscape. While compromise of privileged credentials remains one of the most feared IT threats of an enterprise IT security team, more and more IT incidents are stemming from anomalous end user behavioral profiles. Threat Detection and real-time analytics is a need of the hour.
ARCON | User Behaviour Analytics solution offer enterprise IT security teams with necessary tools to crunch a large lake of enterprise data, spot anomalous and risky behavior profiles along with a capability to trigger alerts in real-time. -
Wrixte SIEM
At Wrixte, we offer a dual AI powered SIEM solution that offers real-time security monitoring, correlation, and analysis of security events and alerts generated by network devices, servers, applications, and other sources. Wrixte SIEM enables organizations to gain 360° visibility into their IT security posture and improve their incident response capabilities.Wrixte SIEM
At Wrixte, we offer a dual AI powered SIEM solution that offers real-time security monitoring, correlation, and analysis of security events and alerts generated by network devices, servers, applications, and other sources. Wrixte SIEM enables organizations to gain 360° visibility into their IT security posture and improve their incident response capabilities.