Product categories
- Application Security
- Automotive Cyber Security
- Cloud Access Security Broker
- Cloud Security
- Cyber Security Services
- Data Security
- Endpoint Security
- Forensics
- Governance Risk Management & Compliance
- Infrastructure Security
- Mobile Security
- Network Security
- Password Manager
- Patch Configuration and Management
- Secure File Transfer
- Secure Web Gateway
- Security Information and Event Management
- Security Training Software
- Unified Threat Management
- User Security
- VAPT
-
Red Team Assessment by Intelidata
Secure your applications against real-world vulnerabilities and run your business with confidence. Maximize security readiness by identifying real world vulnerabilities through rigorous intelligence driven security tests and replicating threat landscapes related to your business. Our Red Team exercises collate and analyze intelligent options which can be used by persistent attackers. We also test your existing security framework for any vulnerabilities to real time attacks.Red Team Assessment by Intelidata
Secure your applications against real-world vulnerabilities and run your business with confidence. Maximize security readiness by identifying real world vulnerabilities through rigorous intelligence driven security tests and replicating threat landscapes related to your business. Our Red Team exercises collate and analyze intelligent options which can be used by persistent attackers. We also test your existing security framework for any vulnerabilities to real time attacks. -
Red Team Assessments
$100.00Red Team engagements can demonstrate the risk posed by an APT (Advanced Persistent Threat). These types of comprehensive, complex security assessments are best used by companies looking to improve the security maturity of the organization.Red Team Assessments
Red Team engagements can demonstrate the risk posed by an APT (Advanced Persistent Threat). These types of comprehensive, complex security assessments are best used by companies looking to improve the security maturity of the organization. -
Red Teaming Assessment by VP Techno Labs
$600.00$550.00Red Teaming Assessment is ideal for medium to larger sized businesses. It is a combination of Social Engineering Testing, Vulnerability Assessment, Attack Simulation Testing and Assessment of Physical security. It uses prevention based approach. We uses some custom made tools along with some open source and commercial tools to cover maximum scope.Red Teaming Assessment by VP Techno Labs
Red Teaming Assessment is ideal for medium to larger sized businesses. It is a combination of Social Engineering Testing, Vulnerability Assessment, Attack Simulation Testing and Assessment of Physical security. It uses prevention based approach. We uses some custom made tools along with some open source and commercial tools to cover maximum scope. -
Regulatory Compliance
The observance of rules, regulations, and norms that are pertinent to an organization's business processes is referred to as regulatory compliance. Processes and strategies for regulatory compliance, offer firms direction as they work to achieve their commercial objectives. Consumers trust businesses that strictly adhere to legal requirements aimed to secure personal data while data breaches tend to continue to occur more frequently in an unprotected environmentRegulatory Compliance
The observance of rules, regulations, and norms that are pertinent to an organization's business processes is referred to as regulatory compliance. Processes and strategies for regulatory compliance, offer firms direction as they work to achieve their commercial objectives. Consumers trust businesses that strictly adhere to legal requirements aimed to secure personal data while data breaches tend to continue to occur more frequently in an unprotected environment -
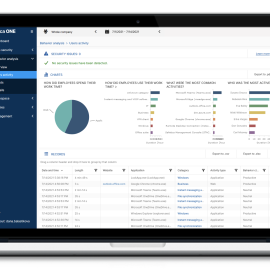
Safetica ONE Discovery+ UEBA
$22.00 – $30.00 for 1 yearIdentify how company data is used and where it is stored and sent, no matter where it resides or flows.- Windows and macOS support
- One-click integration with Microsoft 365
- File content inspection and classification
- Easy to upgrade to the full-featured data security platform
- Runs on bare metal or virtualized on-prem hosted, VM hosted in cloud
Safetica ONE Discovery+ UEBA
Identify how company data is used and where it is stored and sent, no matter where it resides or flows.- Windows and macOS support
- One-click integration with Microsoft 365
- File content inspection and classification
- Easy to upgrade to the full-featured data security platform
- Runs on bare metal or virtualized on-prem hosted, VM hosted in cloud
$22.00 – $30.00 for 1 year -
Safetica ONE Enterprise + UEBA
$45.00 – $62.00 for 1 yearEnterprise data security stack with maximum integration and workflow.- All-in-one data loss prevention & insider threat protection
- The easiest to implement & integrate enterprise DLP
- Advanced workspace control & behaviour analysis
- Very low hardware requirements for servers and device
Safetica ONE Enterprise + UEBA
Enterprise data security stack with maximum integration and workflow.- All-in-one data loss prevention & insider threat protection
- The easiest to implement & integrate enterprise DLP
- Advanced workspace control & behaviour analysis
- Very low hardware requirements for servers and device
$45.00 – $62.00 for 1 year -
Safetica ONE Protection + UEBA
$35.00 – $48.00 for 1 yearBased on the content inspection, internal risk analysis, and clear policies set up for all data channels, Safetica ONE Protection can recognize when somebody makes a mistake or takes chances with your sensitive data. Depending on which mode Safetica ONE is operating in, it can either block the risky activity, notify the admin, or remind the employee about the organization’s security guidelines.Safetica ONE Protection + UEBA
Based on the content inspection, internal risk analysis, and clear policies set up for all data channels, Safetica ONE Protection can recognize when somebody makes a mistake or takes chances with your sensitive data. Depending on which mode Safetica ONE is operating in, it can either block the risky activity, notify the admin, or remind the employee about the organization’s security guidelines.$35.00 – $48.00 for 1 year -
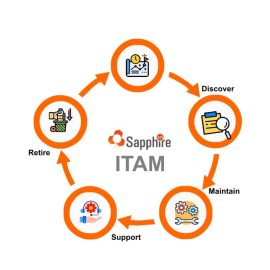
SapphireIMS Asset Lifecycle Management – ITAM
✪ Asset Lifecycle Management with IMAC Processes
✪ Dynamic CMDB Modelling for IT and Non-IT Assets
✪ Bulk Asset Import through Excel File
✪ Contract Management (Warranty, AMC, PO etc.)
✪ Asset Relationship Management
✪ Asset Depreciation
✪ Asset Warranty and AMC Management along with Pre/Post Expiry Notification
✪ Barcode and QR Code Generation
✪ Online and Offline Physical Asset Verification (PAV) through iOS and Android Mobile App and Asset Location Tagging on Map
✪ Asset Reconciliation
✪ Integration with ERP Systems
✪ Dashboards and MIS ReportsSapphireIMS Asset Lifecycle Management – ITAM
✪ Asset Lifecycle Management with IMAC Processes
✪ Dynamic CMDB Modelling for IT and Non-IT Assets
✪ Bulk Asset Import through Excel File
✪ Contract Management (Warranty, AMC, PO etc.)
✪ Asset Relationship Management
✪ Asset Depreciation
✪ Asset Warranty and AMC Management along with Pre/Post Expiry Notification
✪ Barcode and QR Code Generation
✪ Online and Offline Physical Asset Verification (PAV) through iOS and Android Mobile App and Asset Location Tagging on Map
✪ Asset Reconciliation
✪ Integration with ERP Systems
✪ Dashboards and MIS Reports -
SCRUTINY SENSOR
Scrutiny predicts the true nature of files by emulating the static and dynamic behavior in a crypto caged environment and simultaneously training self-learning sensors at the same time to provide accurate verdicts along with detailed analysis in seconds. Our unique approach detects both known and unknown ransomware strains without any reliance on data engrams, centralized signature databases, etc. Also, this stands out as multi-tier, more innovative, and advanced than the other ransomware detection methods available.SCRUTINY SENSOR
Category: Cloud Security Data Security Email Security Endpoint Security Industrial Security Internet of Things Security Malware Detection and Analysis |Scrutiny predicts the true nature of files by emulating the static and dynamic behavior in a crypto caged environment and simultaneously training self-learning sensors at the same time to provide accurate verdicts along with detailed analysis in seconds. Our unique approach detects both known and unknown ransomware strains without any reliance on data engrams, centralized signature databases, etc. Also, this stands out as multi-tier, more innovative, and advanced than the other ransomware detection methods available. -
Seceon aiMSSP
Seceon's aiMSSP combines SOC Dashboard with defense in-depth cybersecurity solution perfected for Automatic Threat Detection and Remediation, making it the most versatile Managed Detection and Response platform in the market.
Build your Managed Security Service business with essential tools, service catalog, onboarding steps and operating procedures. Or, augment your existing SOC with a cyber security solution that is defence in-depth, outcome driven, cutting edge and hassle free. Secure Assets. Gain Trust. Grow Business!Seceon aiMSSP
Seceon's aiMSSP combines SOC Dashboard with defense in-depth cybersecurity solution perfected for Automatic Threat Detection and Remediation, making it the most versatile Managed Detection and Response platform in the market.
Build your Managed Security Service business with essential tools, service catalog, onboarding steps and operating procedures. Or, augment your existing SOC with a cyber security solution that is defence in-depth, outcome driven, cutting edge and hassle free. Secure Assets. Gain Trust. Grow Business! -
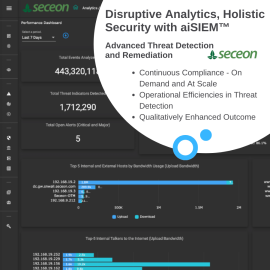
Seceon aiSIEM
Seceon's aiSIEM takes a radically different approach to cybersecurity, ensuring pitfalls of traditional SIEM are averted while empowering enterprises to take on the challenges posed by emerging threat vectors, techniques and tactics.
Protect all your digital assets, people and network round-the-clock at a fraction of the cost. Real time advanced threat detection and auto-remediation with Machine Learning and Artificial Intelligence.Stop the breach and keep business continuity at affordable cost! Catch and neutralize known and unknown threats across your digital assets – on-premise, cloud or remote – before they turn into major incidents.Seceon aiSIEM
Category: Malware Detection and Analysis Security Incident Management and Response Security Information and Event Management |Seceon's aiSIEM takes a radically different approach to cybersecurity, ensuring pitfalls of traditional SIEM are averted while empowering enterprises to take on the challenges posed by emerging threat vectors, techniques and tactics.
Protect all your digital assets, people and network round-the-clock at a fraction of the cost. Real time advanced threat detection and auto-remediation with Machine Learning and Artificial Intelligence.Stop the breach and keep business continuity at affordable cost! Catch and neutralize known and unknown threats across your digital assets – on-premise, cloud or remote – before they turn into major incidents. -
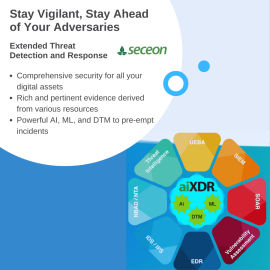
Seceon aiXDR
Seceon’s Extended Detection and Response platform - aiXDR takes grey and white spaces out of the cyber security canvas, leaving nothing to guesswork, abandonment or fate - making it a truly “One Stop Shop” for multi-layered protection against threats, attacks, compromises and exploits.
When it comes to safeguarding digital information, IT assets and business data, IT organizations often contend with quasi-normal state, forced by the lack of deep composite insights from endpoints, servers, firewalls, users, entity behaviors, network traffic, vulnerabilities and threat intelligence. Secure your final frontiers – whether in the remote workplace, in the cloud, in the office or in transit – with Seceon aiXDR. Draw upon insights rendered by razor-sharp analytics, guided by AI and ML.Seceon aiXDR
Seceon’s Extended Detection and Response platform - aiXDR takes grey and white spaces out of the cyber security canvas, leaving nothing to guesswork, abandonment or fate - making it a truly “One Stop Shop” for multi-layered protection against threats, attacks, compromises and exploits.
When it comes to safeguarding digital information, IT assets and business data, IT organizations often contend with quasi-normal state, forced by the lack of deep composite insights from endpoints, servers, firewalls, users, entity behaviors, network traffic, vulnerabilities and threat intelligence. Secure your final frontiers – whether in the remote workplace, in the cloud, in the office or in transit – with Seceon aiXDR. Draw upon insights rendered by razor-sharp analytics, guided by AI and ML. -
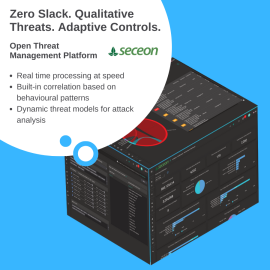
Seceon Open Threat Management Platform
Seceon’s Open Threat Management Platform makes the best out of available information and intelligence from various digital assets – guided by ML based behavioral analytics and AI based decision-making – to raise and eliminate only the qualified cyber security threats, proactively and confidently.By leveraging cutting edge technologies, the platform brings best-of-breed cyber threat detection techniques, visualization, remediation and reporting with 75%-90% reduction in Capex and Opex.
Seceon’s Open Threat Management Platform strikes a fine balance between automation, visibility, insights and custom controls. OTM optimizes analytics, reduces time-to-detection, time-to-remediation and provides control mechanisms to enforce network policies for micro-segmentation and custom user-defined-alerts.
Seceon Open Threat Management Platform
Seceon’s Open Threat Management Platform makes the best out of available information and intelligence from various digital assets – guided by ML based behavioral analytics and AI based decision-making – to raise and eliminate only the qualified cyber security threats, proactively and confidently.By leveraging cutting edge technologies, the platform brings best-of-breed cyber threat detection techniques, visualization, remediation and reporting with 75%-90% reduction in Capex and Opex.
Seceon’s Open Threat Management Platform strikes a fine balance between automation, visibility, insights and custom controls. OTM optimizes analytics, reduces time-to-detection, time-to-remediation and provides control mechanisms to enforce network policies for micro-segmentation and custom user-defined-alerts.
-
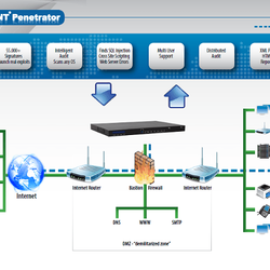
SecPoint Penetrator – VAPT
$250.00 – $12,750.00 / yearSecPoint Penetrator can help you to find the vulnerabilities on your entire network. You can scan your internal local IP addresses and your public IPs available on the Internet. You can scan your Websites, webapps, servers, workstations, IoT, scada etc. Find all SSL vulnarabilities. SecPoint State of the art Cyber Security and must have for every organization. SecPoint can be installed as harware appliance or virtual machine.- Discover your weak points before it is too late.
- Ultimate Vulnerability Scanning
- Distributed Scanning Capability. Master / Client mode.
- Hardware 1U Rack or Virtual ESXi,Hyper-V,Linux Images
- Build in Ticket System
- Multiple Reporting: Consultant, Tech, Executive
- Multiple Report Formats: PDF, HTML & XML
- Not fixed on IP adresses, scan unlimited IPs, buy license for simultanous scan
SecPoint Penetrator – VAPT
SecPoint Penetrator can help you to find the vulnerabilities on your entire network. You can scan your internal local IP addresses and your public IPs available on the Internet. You can scan your Websites, webapps, servers, workstations, IoT, scada etc. Find all SSL vulnarabilities. SecPoint State of the art Cyber Security and must have for every organization. SecPoint can be installed as harware appliance or virtual machine.- Discover your weak points before it is too late.
- Ultimate Vulnerability Scanning
- Distributed Scanning Capability. Master / Client mode.
- Hardware 1U Rack or Virtual ESXi,Hyper-V,Linux Images
- Build in Ticket System
- Multiple Reporting: Consultant, Tech, Executive
- Multiple Report Formats: PDF, HTML & XML
- Not fixed on IP adresses, scan unlimited IPs, buy license for simultanous scan
$250.00 – $12,750.00 / year -
Securaa – Security Automation Platform
Securaa is a Comprehensive No Code Security Automation Platform that blends intelligence, risk-based asset management, vulnerability insights, automation and incident response into a single platform enabling SOC’s to reduce cybersecurity response time significantly and increase throughput manifolds.- Best RoI in the industry
- Reduce response time by over 95%
- Increase productivity by 300%
- Automate 100% L1 tasks
- Implement in weeks
- Build new playbook in hours
Securaa – Security Automation Platform
Securaa is a Comprehensive No Code Security Automation Platform that blends intelligence, risk-based asset management, vulnerability insights, automation and incident response into a single platform enabling SOC’s to reduce cybersecurity response time significantly and increase throughput manifolds.- Best RoI in the industry
- Reduce response time by over 95%
- Increase productivity by 300%
- Automate 100% L1 tasks
- Implement in weeks
- Build new playbook in hours
-
SecurDPS Connect
SecurDPS Connect allows users to develop customized templates which train the solution to detect and replace sensitive data with encrypted or tokenized data before that information is stored in the application or cloud service. These templates provide the mechanism to define what types of information are sensitive and guide the type of protection for each data field.SecurDPS Connect
SecurDPS Connect allows users to develop customized templates which train the solution to detect and replace sensitive data with encrypted or tokenized data before that information is stored in the application or cloud service. These templates provide the mechanism to define what types of information are sensitive and guide the type of protection for each data field.