Product categories
- Application Security
- Automotive Cyber Security
- Cloud Access Security Broker
- Cloud Security
- Cyber Security Services
- Data Security
- Endpoint Security
- Forensics
- Governance Risk Management & Compliance
- Infrastructure Security
- Mobile Security
- Network Security
- Password Manager
- Patch Configuration and Management
- Secure File Transfer
- Secure Web Gateway
- Security Information and Event Management
- Security Training Software
- Unified Threat Management
- User Security
- VAPT
-
PlainID Partner Manager
PlainID Partner Manager revolutionizes B2B Access Management (also known as Partner IAM or PIAM) by letting you manage your partners as “organizations,” while delegating admin capabilities, so your partners can manage their own users’ access.
PlainID Partner Manager
PlainID Partner Manager revolutionizes B2B Access Management (also known as Partner IAM or PIAM) by letting you manage your partners as “organizations,” while delegating admin capabilities, so your partners can manage their own users’ access.
-
PlainID Policy Manager
PlainID’s Policy Manager gives you centralized management in a decentralized enforcement architecture. You get a focused view along with the ability to control who has access to what, across your digital landscape. It also provides improved visibility of access risks through advanced access control analytics. This allows a company to have predictive and prescriptive access controls, as well as run-time authorization enforcement using Policy-Based Access Control (PBAC) capabilities with workflows and SOD controls. It integrates with leading vendors in the IAM space such as SailPoint, Okta and Azure AD.
PlainID Policy Manager
PlainID’s Policy Manager gives you centralized management in a decentralized enforcement architecture. You get a focused view along with the ability to control who has access to what, across your digital landscape. It also provides improved visibility of access risks through advanced access control analytics. This allows a company to have predictive and prescriptive access controls, as well as run-time authorization enforcement using Policy-Based Access Control (PBAC) capabilities with workflows and SOD controls. It integrates with leading vendors in the IAM space such as SailPoint, Okta and Azure AD.
-
Plurilock AI Cloud DLP
Plurilock AI Cloud DLP secures your users, software, and data seamlessly.- Single sign-on.
- Access control.
- Cloud least privilege.
- Data loss prevention.
- Workday control.
- Identity sanity.
Plurilock AI Cloud DLP
Plurilock AI Cloud DLP secures your users, software, and data seamlessly.- Single sign-on.
- Access control.
- Cloud least privilege.
- Data loss prevention.
- Workday control.
- Identity sanity.
-
Privilege Access Management
Built to address the evolving privileged access use-case challenges, ARCON | PAM offers best-in-class access control features. A feature-rich solution, ARCON | PAM offers an IT security team with the deepest level of granular controls and Just-in-time (JIT) privileged access to enforce the principle of least privilege in any IT environment.
Trusted by more than 1000 global organizations, spanning wide-ranging industries, the enterprise-grade solution offers a best-fit architecture to ensure scalability, IT efficiency and privileged access security including compliance.
Privilege Access Management
Built to address the evolving privileged access use-case challenges, ARCON | PAM offers best-in-class access control features. A feature-rich solution, ARCON | PAM offers an IT security team with the deepest level of granular controls and Just-in-time (JIT) privileged access to enforce the principle of least privilege in any IT environment.
Trusted by more than 1000 global organizations, spanning wide-ranging industries, the enterprise-grade solution offers a best-fit architecture to ensure scalability, IT efficiency and privileged access security including compliance.
-
Privileged Access Management for System by Netand
HIWARE Privileged Access Management for System enables the complete management and supervision of users by controlling all accesses to and operations of the IT infrastructure operating system such as network and server, monitoring work details in realtime and saving log records.Privileged Access Management for System by Netand
HIWARE Privileged Access Management for System enables the complete management and supervision of users by controlling all accesses to and operations of the IT infrastructure operating system such as network and server, monitoring work details in realtime and saving log records. -
ProDiscover
Platform for identification of look-alike mail domains. Proactive detection of look-alike domains through 14 types of domain variations.ProDiscover
Platform for identification of look-alike mail domains. Proactive detection of look-alike domains through 14 types of domain variations. -
ProDMARC
Implement email authentication with PRODMARC
ProDMARC acts as the shield of any organisation from e-mail based spoofing attacks that impact your brand and hence, your revenues. ProDMARC helps improve customer and third party trust in your email.- Protect your brand against impersonation
- Gain visibility of your email activities
- Improve Deliverability of Email
- Generate actionable threat intelligence
ProDMARC
Implement email authentication with PRODMARC
ProDMARC acts as the shield of any organisation from e-mail based spoofing attacks that impact your brand and hence, your revenues. ProDMARC helps improve customer and third party trust in your email.- Protect your brand against impersonation
- Gain visibility of your email activities
- Improve Deliverability of Email
- Generate actionable threat intelligence
-
ProNoesis Defend – Managed Services for IAM
ProNoesis Defend IAM Managed Services team, not only ensures performance and availability of IAM systems but also keep system updated, securely managed and monitor round the clock IAM processes to protect identities.
We provide continues improvement and automation adding visibility by reducing risk and cost.ProNoesis Defend – Managed Services for IAM
ProNoesis Defend IAM Managed Services team, not only ensures performance and availability of IAM systems but also keep system updated, securely managed and monitor round the clock IAM processes to protect identities.
We provide continues improvement and automation adding visibility by reducing risk and cost. -
ProNoesis Define – Advisory and Consulting Services for IAM
We can help you turn your vision of an Identity and Access Management program into a reality. Our extensive experience with a variety of IAM technologies and proven approach is designed to deliver a pragmatic strategy & roadmap to implement a secure identity environment.ProNoesis Define – Advisory and Consulting Services for IAM
We can help you turn your vision of an Identity and Access Management program into a reality. Our extensive experience with a variety of IAM technologies and proven approach is designed to deliver a pragmatic strategy & roadmap to implement a secure identity environment. -
ProNoesis Deliver – Implementation & Integration Services for IAM
Our proven delivery methodology leverages best practices and DevOps to accelerate the implementation process and minimize integration overhead.
Traditional IAM implementation are too complex, needs manual intervention, lead to increased risk and fail to adapt organization changes. Our methodology is to build strong IAM framework compromised of standards, templates and process that applications will follow to onboard using integration patterns.
ProNoesis Deliver – Implementation & Integration Services for IAM
Our proven delivery methodology leverages best practices and DevOps to accelerate the implementation process and minimize integration overhead.
Traditional IAM implementation are too complex, needs manual intervention, lead to increased risk and fail to adapt organization changes. Our methodology is to build strong IAM framework compromised of standards, templates and process that applications will follow to onboard using integration patterns.
-
ProPATROL
Platform for facilitating employees to report phishing attacks. One-click reporter integrated with mailbox having incident analysis and ticketing capabilities.ProPATROL
Platform for facilitating employees to report phishing attacks. One-click reporter integrated with mailbox having incident analysis and ticketing capabilities. -
Prophaze – Native Cloud Security Platform k8s
Prophaze WAF secures your Web Assets from OWASP Top 10 Vulnerabilities by running both as SAAS and On Prem deployment. Prophaze First native cloud security platform. It will block all the attacks targeting your Web Application in cloud & go live in 15 minutes.Prophaze – Native Cloud Security Platform k8s
Prophaze WAF secures your Web Assets from OWASP Top 10 Vulnerabilities by running both as SAAS and On Prem deployment. Prophaze First native cloud security platform. It will block all the attacks targeting your Web Application in cloud & go live in 15 minutes. -
ProPHISH
Arm your employees against phishing attacks
ProPHISH is a highly effective simulation based solution for training and identifying employees of your organization, who might be susceptible to targeted Phishing Attacks. platform to help identify and train employees who are susceptible to targeted phishing.ProPHISH
Arm your employees against phishing attacks
ProPHISH is a highly effective simulation based solution for training and identifying employees of your organization, who might be susceptible to targeted Phishing Attacks. platform to help identify and train employees who are susceptible to targeted phishing. -
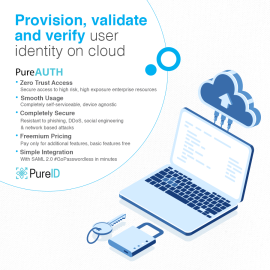
PureAUTH – The best Passwordless SSO Solution
PureAUTH is a SaaS based passwordless SSO platform. Completely self-serviceable & easy to deploy, PureAUTH is the most resilient passwordless authentication solution in the market.PureAUTH – The best Passwordless SSO Solution
PureAUTH is a SaaS based passwordless SSO platform. Completely self-serviceable & easy to deploy, PureAUTH is the most resilient passwordless authentication solution in the market. -
RADARK
KELA’s RADARK delivers automated threat intelligence, cultivating the targeted and contextualized insights – at scale – that you need to stay ahead of attackers. Automatically monitor your environment and ensure that targeted threats are mitigated immediately to consistently maintain a strong security posture.RADARK
KELA’s RADARK delivers automated threat intelligence, cultivating the targeted and contextualized insights – at scale – that you need to stay ahead of attackers. Automatically monitor your environment and ensure that targeted threats are mitigated immediately to consistently maintain a strong security posture. -
Reblaze WAAP
About Reblaze: Reblaze provides a complete, cloud-based, comprehensive and proactive protection shield for web platforms (websites/web applications/API), together with a command and control system. We offer an all-in-one private virtual cloud-based solution (VPC) that includes IPS/WAF, DoS/DDoS protection, BOT detection and exclusion, anti-scraping, CDN and more. As a result of our unique approach, we monitor and cleanse the traffic before it reaches our customers' websites, and we can easily work with existing security solutions. The service requires a five-minute setup, zero installation, a single DNS change and can be deployed even under an attack. Service can be stopped at any stage and with a Try and Buy period of 30 days. We're fully integrated with AWS, GCP, and Azure, being able to build our platform in the clients' environment, ensuring privacy, enhancing the cloud's latency and efficiency, and also, reducing costs of traffic.Reblaze WAAP
About Reblaze: Reblaze provides a complete, cloud-based, comprehensive and proactive protection shield for web platforms (websites/web applications/API), together with a command and control system. We offer an all-in-one private virtual cloud-based solution (VPC) that includes IPS/WAF, DoS/DDoS protection, BOT detection and exclusion, anti-scraping, CDN and more. As a result of our unique approach, we monitor and cleanse the traffic before it reaches our customers' websites, and we can easily work with existing security solutions. The service requires a five-minute setup, zero installation, a single DNS change and can be deployed even under an attack. Service can be stopped at any stage and with a Try and Buy period of 30 days. We're fully integrated with AWS, GCP, and Azure, being able to build our platform in the clients' environment, ensuring privacy, enhancing the cloud's latency and efficiency, and also, reducing costs of traffic.