Product categories
- Application Security
- Automotive Cyber Security
- Cloud Access Security Broker
- Cloud Security
- Cyber Security Services
- Data Security
- Endpoint Security
- Forensics
- Governance Risk Management & Compliance
- Infrastructure Security
- Mobile Security
- Network Security
- Password Manager
- Patch Configuration and Management
- Secure File Transfer
- Secure Web Gateway
- Security Information and Event Management
- Security Training Software
- Unified Threat Management
- User Security
- VAPT
-
ISMAC SOAR
$29.99$25.99 / year with a 14-day free trial and a $6,000.00 sign-up feeFor large and complex environments ISMAC SOAR will enable your team to achieve scalability of your cyberdefense efforts.ISMAC SOAR
Category: Cloud Security Compliance Management Container Security Log Management Malware Detection and Analysis Security Incident Management and Response SOAR Threat Intelligence and Signature Feeds VAPT | SKU: 003For large and complex environments ISMAC SOAR will enable your team to achieve scalability of your cyberdefense efforts.$25.99Was $29.99Save $4 -
ISMS Services by SecurDefense
$8,000.00SecurDefense services to define the polices for implementing ISMS or ISO27001, perform the GAP analysis as per the ISMS Policies and reassessment of the Security policies as ISMS Standards and Controls.ISMS Services by SecurDefense
SecurDefense services to define the polices for implementing ISMS or ISO27001, perform the GAP analysis as per the ISMS Policies and reassessment of the Security policies as ISMS Standards and Controls. -
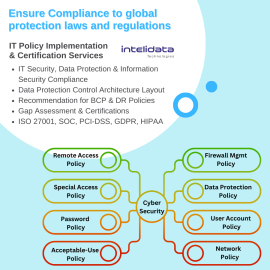
IT Policy and Certification Services by Intelidata
Review & Implementation of IS/IT Policies and IS/IT controls for their adequacy and effectiveness vis-à-vis frameworks/standards of ISO 27001:2022, IT Act 2008 & Cert-in guidelines.- IT Security, Data Protection & Information Security Compliance's Control Implementation
- Data Protection Control Architecture Layout as per new emerging Cyber Risks & Threats
- Recommendation for BCP & DR policies
- ISMS and Information Security Awareness Trainings for IT Staff
IT Policy and Certification Services by Intelidata
Review & Implementation of IS/IT Policies and IS/IT controls for their adequacy and effectiveness vis-à-vis frameworks/standards of ISO 27001:2022, IT Act 2008 & Cert-in guidelines.- IT Security, Data Protection & Information Security Compliance's Control Implementation
- Data Protection Control Architecture Layout as per new emerging Cyber Risks & Threats
- Recommendation for BCP & DR policies
- ISMS and Information Security Awareness Trainings for IT Staff
-
JuicyScore
Prevent fraudulent activities, reduce the risk of threats and gain new clients with sustainable portfolio growth. JuicyScore allows identifying different types of fraud, shady behaviour and users' intentions, segmenting the incoming flow upon risk level, raising the informative value and resolution of your decision-making systems.JuicyScore
Prevent fraudulent activities, reduce the risk of threats and gain new clients with sustainable portfolio growth. JuicyScore allows identifying different types of fraud, shady behaviour and users' intentions, segmenting the incoming flow upon risk level, raising the informative value and resolution of your decision-making systems. -
Kount Central
Protect merchants from digital fraud with one integration
Through Kount Central, you can offer industry-leading digital fraud protection — and access to the largest global network of fraud and trust-related signals — to your entire merchant portfolio. Kount Central is built on our AI-driven fraud prevention solution, Kount CommandKount Central
Protect merchants from digital fraud with one integration
Through Kount Central, you can offer industry-leading digital fraud protection — and access to the largest global network of fraud and trust-related signals — to your entire merchant portfolio. Kount Central is built on our AI-driven fraud prevention solution, Kount Command -
Kount Command
Kount Command delivers accurate identity trust decisions in milliseconds. Automatically approve, decline, or hold transactions and customize business policies to refine fraud prevention strategies. Advanced AI and machine learning models detect emerging fraud and uncover anomalies without adding friction to the customer experience. Merchants can stop losing money to fraud and accept more good orders.Kount Command
Kount Command delivers accurate identity trust decisions in milliseconds. Automatically approve, decline, or hold transactions and customize business policies to refine fraud prevention strategies. Advanced AI and machine learning models detect emerging fraud and uncover anomalies without adding friction to the customer experience. Merchants can stop losing money to fraud and accept more good orders. -
Kount Control
Kount Control prevents account takeover attacks by detecting high-velocity attacks from bots, credential stuffing, and other malicious activities. Plus, Kount Control customers can manage trusted devices and track failed login attempt data to improve account protection policies.
The account takeover solution combines machine learning, device intelligence , and customizable business policies to identify risky login behavior in real time. Whether from credential stuffing, card testing, bot attacks, or other abnormal activities, Kount Control challenges high-risk behavior and reduces friction for good customers.
Kount Control
Category: Fraud Prevention Identity Theft Detection Multi Factor Authentication | SKU: KOUNT-CONTROLKount Control prevents account takeover attacks by detecting high-velocity attacks from bots, credential stuffing, and other malicious activities. Plus, Kount Control customers can manage trusted devices and track failed login attempt data to improve account protection policies.
The account takeover solution combines machine learning, device intelligence , and customizable business policies to identify risky login behavior in real time. Whether from credential stuffing, card testing, bot attacks, or other abnormal activities, Kount Control challenges high-risk behavior and reduces friction for good customers.
-
Kratikal Vulnerability Assessment & Penetration Testing Service
Kratikal, being a CERT-In Empanelled, provides a Vulnerability Assessment and Penetration Testing (VAPT) security service that focuses on discovering flaws in network, server, and system infrastructure. Organizational security is the emphasis of vulnerability assessment, whereas real-world exploitation is the objective of penetration testing.
Kratikal Vulnerability Assessment & Penetration Testing Service
Kratikal, being a CERT-In Empanelled, provides a Vulnerability Assessment and Penetration Testing (VAPT) security service that focuses on discovering flaws in network, server, and system infrastructure. Organizational security is the emphasis of vulnerability assessment, whereas real-world exploitation is the objective of penetration testing.
-
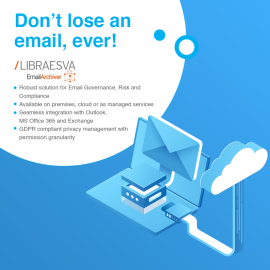
Libraesva Email Archiver
$3,640.00 – $6,930.00 / yearLibraesva Email Archiver is ready for your network— on premise, cloud or as managed service, thanks to the native multi-tenant features and a complete API that enables full integration with any environment.Libraesva Email Archiver is a powerful and simple solution for email Governance, Risk and Compliance; up and running in minutes creates 1:1 copies of all emails in a central email archive to ensure the security and availability of large amounts of data over a period of years.
No matter what email server you are using, either in the cloud or on premise: Libraesva Email Archiver seamless integrates with any mail server, and offers native integration with Office 365 and Microsoft Exchange.Thanks to the exclusive Outlook Add-In, that supports both Windows and Mac, users can still access their archived email in the usual way.
Libraesva Email Archiver
Libraesva Email Archiver is ready for your network— on premise, cloud or as managed service, thanks to the native multi-tenant features and a complete API that enables full integration with any environment.Libraesva Email Archiver is a powerful and simple solution for email Governance, Risk and Compliance; up and running in minutes creates 1:1 copies of all emails in a central email archive to ensure the security and availability of large amounts of data over a period of years.
No matter what email server you are using, either in the cloud or on premise: Libraesva Email Archiver seamless integrates with any mail server, and offers native integration with Office 365 and Microsoft Exchange.Thanks to the exclusive Outlook Add-In, that supports both Windows and Mac, users can still access their archived email in the usual way.
$3,640.00 – $6,930.00 / year -
Libraesva Email Security Gateway
$5.80 – $27.75 / yearLibraesva ESG is an Integrated Email Security Solution. We deliver advanced security for cloud-based email platforms. Email Security Gateway protects Microsoft 365 and Google Workspace using multiple layers of protection, both at the Gateway and API layers, so multiple solutions are not needed. Email threats like phishing attacks, email fraud, and Business Email Compromise (BEC) are stopped before reaching their target. Simple and easy to deploy configurations guarantee that customized email protection is in place in a matter of minutes. Depending on your needs, you have the option to run in the cloud or on-premise. Cloud instances of Libraesva ESG are the most secure in the industry thanks to our dedicated, private cloud deployments. There is no need to worry about shared environments or certificates.Libraesva Email Security Gateway
Libraesva ESG is an Integrated Email Security Solution. We deliver advanced security for cloud-based email platforms. Email Security Gateway protects Microsoft 365 and Google Workspace using multiple layers of protection, both at the Gateway and API layers, so multiple solutions are not needed. Email threats like phishing attacks, email fraud, and Business Email Compromise (BEC) are stopped before reaching their target. Simple and easy to deploy configurations guarantee that customized email protection is in place in a matter of minutes. Depending on your needs, you have the option to run in the cloud or on-premise. Cloud instances of Libraesva ESG are the most secure in the industry thanks to our dedicated, private cloud deployments. There is no need to worry about shared environments or certificates.$5.80 – $27.75 / year -
Libraesva PhishBrain
$3.45 – $11.76 / yearPhishing Awareness on your terms, not theirs!
Libraesva PhishBrain analyzes each employee and organization, profiling each on an ongoing basis to determine their phishing risk profile. PhishBrain identifies the highest risk employees and tracks their progress over time, in order to become a truly security-conscious company. Key features include:- SAAS based
- Office 365 and G-suite native integration
- User friendly
- Better insight
Libraesva PhishBrain
Phishing Awareness on your terms, not theirs!
Libraesva PhishBrain analyzes each employee and organization, profiling each on an ongoing basis to determine their phishing risk profile. PhishBrain identifies the highest risk employees and tracks their progress over time, in order to become a truly security-conscious company. Key features include:- SAAS based
- Office 365 and G-suite native integration
- User friendly
- Better insight
$3.45 – $11.76 / year -
Maritime Cybersecurity Awareness Course
We also offer cybersecurity awareness courses specially crafted for maritime industry. https://athena-dynamics-academy.trainercentral.com/course/maritime-cyber-security-awareness-course#/homeMaritime Cybersecurity Awareness Course
We also offer cybersecurity awareness courses specially crafted for maritime industry. https://athena-dynamics-academy.trainercentral.com/course/maritime-cyber-security-awareness-course#/home -
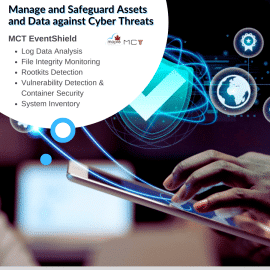
MCT EventShield
A MCT EventShield tool is crucial for organizations to monitor and safeguard their assets and data against cyber threats. MCT EventShield functions by collecting security-related data from various sources, such as logs, network traffic, and other security tools.MCT EventShield
A MCT EventShield tool is crucial for organizations to monitor and safeguard their assets and data against cyber threats. MCT EventShield functions by collecting security-related data from various sources, such as logs, network traffic, and other security tools. -
Media Sonar Web Intelligence & Investigation Platform
$28,785.00 / year with a 3-day free trialMedia Sonar is an all-in-one Web Intelligence and Investigation Platform. Our solution broadens the lens of your digital attack surface, securing your brand and assets while strengthen your security operations posture. Equip your security team with visibility into indicators of threat emerging outside of your organization, with intelligence from the Open and Dark Web. Media Sonar works with our clients and partners to deliver personalized 1:1 customer training and support. All questions answered, period.Media Sonar Web Intelligence & Investigation Platform
Media Sonar is an all-in-one Web Intelligence and Investigation Platform. Our solution broadens the lens of your digital attack surface, securing your brand and assets while strengthen your security operations posture. Equip your security team with visibility into indicators of threat emerging outside of your organization, with intelligence from the Open and Dark Web. Media Sonar works with our clients and partners to deliver personalized 1:1 customer training and support. All questions answered, period.$28,785.00 / year with a 3-day free trial -
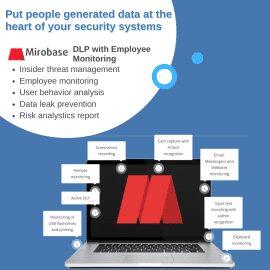
Mirobase DLP with Employee Monitoring
Lets not just call Mirobase an Employee Monitoring solution, its much more than that. Mirobase can improve productivity, increase revenue, improve profits and safeguard data. Mirobase can be used for- Insider Threat Management
- Employee Monitoring
- User Behavior Analysis - Finding Disloyal Employees, Getting to know in advance who wants to leave job
- Data Leak Prevention
- User management
- Endpoint management
- Most importantly Safeguard Confidential & Crucial Data
Mirobase DLP with Employee Monitoring
Lets not just call Mirobase an Employee Monitoring solution, its much more than that. Mirobase can improve productivity, increase revenue, improve profits and safeguard data. Mirobase can be used for- Insider Threat Management
- Employee Monitoring
- User Behavior Analysis - Finding Disloyal Employees, Getting to know in advance who wants to leave job
- Data Leak Prevention
- User management
- Endpoint management
- Most importantly Safeguard Confidential & Crucial Data
-
Mobile Application Penetration Testiing
$110.00Our mobile security testing services combine static and behavioral analysis to deliver full visibility into flaws in applications in real-time. Our services are easy to use and highly accurate, helping to avoid false positives and providing step-by-step guidance to remediate vulnerabilities found during security testing. With our services, development teams can meet the demands of regulatory frameworks more quickly and with less effort.Mobile Application Penetration Testiing
Our mobile security testing services combine static and behavioral analysis to deliver full visibility into flaws in applications in real-time. Our services are easy to use and highly accurate, helping to avoid false positives and providing step-by-step guidance to remediate vulnerabilities found during security testing. With our services, development teams can meet the demands of regulatory frameworks more quickly and with less effort.