Onefede > Products
Product categories
- Application Security
- Automotive Cyber Security
- Cloud Access Security Broker
- Cloud Security
- Cyber Security Services
- Data Security
- Endpoint Security
- Forensics
- Governance Risk Management & Compliance
- Infrastructure Security
- Mobile Security
- Network Security
- Password Manager
- Patch Configuration and Management
- Secure File Transfer
- Secure Web Gateway
- Security Information and Event Management
- Security Training Software
- Unified Threat Management
- User Security
- VAPT
-
Indusface Mobile Application Scanner
Indusface Mobile Application Scanning helps businesses secure their apps with in-depth testing. It detects vulnerabilities and insecure permission issues to provide comprehensive reports on readiness of apps to be used on mobile devices safely. With mobile devices and applications becoming the next-big-step for businesses, Indusface Mobile Application Scanning (MAS) helps you take control over their security. It uses a broad combination of mobile application security assessment techniques to find out malware, data leakage, and fraudulent transaction risks.A Dynamic Mobile Application Security Penetration Testing Solution from IndusfaceIndusface Mobile Application Scanner
Indusface Mobile Application Scanning helps businesses secure their apps with in-depth testing. It detects vulnerabilities and insecure permission issues to provide comprehensive reports on readiness of apps to be used on mobile devices safely. With mobile devices and applications becoming the next-big-step for businesses, Indusface Mobile Application Scanning (MAS) helps you take control over their security. It uses a broad combination of mobile application security assessment techniques to find out malware, data leakage, and fraudulent transaction risks.A Dynamic Mobile Application Security Penetration Testing Solution from Indusface -
Indusface Web Application Scanner
Comprehensive, In-Depth & Managed Application Security Testing Indusface WAS Premium is offered as a SaaS-based solution, and provides real-time reports and summaries based on type and severity of vulnerabilities through the dashboard. It is designed to help organizations manage security across multiple web applications with daily or on-demand auditing, defacement protection and blacklisting detection Indusface WAS Premium provides comprehensive dynamic application security testing (DAST). It combines automated web application scanning to detect OWASP Top 10 and malwares along with CERT-In certified security expert validation for comprehensive analysis on business logic flaws and other complex vulnerabilities. Our managed security team also provides in-depth verification and demonstration of business impacts of the complex vulnerabilities.Indusface Web Application Scanner
Comprehensive, In-Depth & Managed Application Security Testing Indusface WAS Premium is offered as a SaaS-based solution, and provides real-time reports and summaries based on type and severity of vulnerabilities through the dashboard. It is designed to help organizations manage security across multiple web applications with daily or on-demand auditing, defacement protection and blacklisting detection Indusface WAS Premium provides comprehensive dynamic application security testing (DAST). It combines automated web application scanning to detect OWASP Top 10 and malwares along with CERT-In certified security expert validation for comprehensive analysis on business logic flaws and other complex vulnerabilities. Our managed security team also provides in-depth verification and demonstration of business impacts of the complex vulnerabilities. -
Information Archive
Information Archiving helps organisations meet GDPR and other regulatory requirements by securing and managing critical data. The solution stores an unlimited number of files and communications across email, SMS, and emerging platforms like Microsoft Teams and social media. It helps protect your organisation against compliance violations and unplanned litigations and is an essential replacement for organisations moving off of aging, on-premises, email-only hardware.Information Archive
Category: Cloud Security Compliance Management Cyber Security Services Data Breach Protection Data Discovery Data Security |Information Archiving helps organisations meet GDPR and other regulatory requirements by securing and managing critical data. The solution stores an unlimited number of files and communications across email, SMS, and emerging platforms like Microsoft Teams and social media. It helps protect your organisation against compliance violations and unplanned litigations and is an essential replacement for organisations moving off of aging, on-premises, email-only hardware. -
Information Security Risk Assessment
$100.00Performing a comprehensive Risk Assessment on the identified critical IT assets would enable the selection of appropriate risk mitigation controls. Intect’s Risk assessment methodology is a multi-fold activity comprising assigning values to the identified critical information assets, threat assessment, & gap analysisInformation Security Risk Assessment
Performing a comprehensive Risk Assessment on the identified critical IT assets would enable the selection of appropriate risk mitigation controls. Intect’s Risk assessment methodology is a multi-fold activity comprising assigning values to the identified critical information assets, threat assessment, & gap analysis -
INTELACT
INTELACT offers organizations a fully automated and targeted solution for Attack Surface Monitoring, enabling tailored configuration of client’s assets, automated monitoring of these assets in KELA’s Dark Net sources, and real-time alerting on any compromise or exposure of themINTELACT
INTELACT offers organizations a fully automated and targeted solution for Attack Surface Monitoring, enabling tailored configuration of client’s assets, automated monitoring of these assets in KELA’s Dark Net sources, and real-time alerting on any compromise or exposure of them -
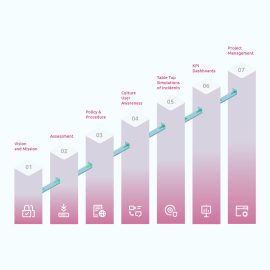
Invinsense Compliance
Invinsense GSOS solutions and services help your organizations achieve the necessary compliance needed because of your industry and geography. Our intuitive solution and expert Pink team help you implement frameworks like ISO, NIST, SOC-2, etc without the frustration of complexity and confusion of documentation. We help you achieve smooth processes, documentation and needed awareness to achieve not only compliance, but also preparedness of any scale of cyberattack. We help you achieve peace of mind to continue doing your core business.Invinsense Compliance
Invinsense GSOS solutions and services help your organizations achieve the necessary compliance needed because of your industry and geography. Our intuitive solution and expert Pink team help you implement frameworks like ISO, NIST, SOC-2, etc without the frustration of complexity and confusion of documentation. We help you achieve smooth processes, documentation and needed awareness to achieve not only compliance, but also preparedness of any scale of cyberattack. We help you achieve peace of mind to continue doing your core business. -
Invinsense MDR
INVINSENSE MDR DO DETECTION, THREAT HUNTING, AND RESPONSE FOR CISOS The main objective of Invinsense MDR is to identify potentially malicious activities across your technology landscape and neutralize them on behalf of CISOs or incoordination of CISOInvinsense MDR
INVINSENSE MDR DO DETECTION, THREAT HUNTING, AND RESPONSE FOR CISOS The main objective of Invinsense MDR is to identify potentially malicious activities across your technology landscape and neutralize them on behalf of CISOs or incoordination of CISO -
Invinsense MDR+
Invinsense Managed Detection and Response Plus Invinsense MDR+ - MDR Services That Leverage Deception, Patch Management and Network Intrusion Detection System (NIDS)Invinsense MDR+
Invinsense Managed Detection and Response Plus Invinsense MDR+ - MDR Services That Leverage Deception, Patch Management and Network Intrusion Detection System (NIDS) -
Invinsense OMDR
Invinsense Offensive Managed Detection and Response helps organization to test their cybersecurity tools, people and processes with the help of our te Red Team that thinks and acts like attacker. Fled team who manages Invinsense MDR will help your cybersecurity to observe the entry of adversaries, lateral movements attack paths and weaknesses in IT systems and networks.Invinsense OMDR
Invinsense Offensive Managed Detection and Response helps organization to test their cybersecurity tools, people and processes with the help of our te Red Team that thinks and acts like attacker. Fled team who manages Invinsense MDR will help your cybersecurity to observe the entry of adversaries, lateral movements attack paths and weaknesses in IT systems and networks. -
Invinsense OXDR
Cybersecurity is a continuous journey as attacks are a continuous process. This journey starts with having cybersecurity solutions that act as basic hygiene and provide preventive cybersecurity. Then comes detection and prevention, threat hunting and solutions and people needed for it. Once everything is done, organizations achieve a certain cybersecurity posture. Majority of the organizations stop here and a few go to test their cybersecurity posture and very rare an organization goes beyond that and put its cybersecurity to continuous testing and implementing those results in achieving a cybersecurity posture that is dynamic and in response to the environment.Invinsense OXDR
Cybersecurity is a continuous journey as attacks are a continuous process. This journey starts with having cybersecurity solutions that act as basic hygiene and provide preventive cybersecurity. Then comes detection and prevention, threat hunting and solutions and people needed for it. Once everything is done, organizations achieve a certain cybersecurity posture. Majority of the organizations stop here and a few go to test their cybersecurity posture and very rare an organization goes beyond that and put its cybersecurity to continuous testing and implementing those results in achieving a cybersecurity posture that is dynamic and in response to the environment. -
Invinsense XDR
Invensense XDR is one of the most integrated XDR that combines the intelligence of the key cybersecurity solutions SIEM, SOARL EDR, Case Management, Threat Intelligence, Threat Exchange, and other cybersecurity solutions.Invinsense XDR
Invensense XDR is one of the most integrated XDR that combines the intelligence of the key cybersecurity solutions SIEM, SOARL EDR, Case Management, Threat Intelligence, Threat Exchange, and other cybersecurity solutions. -
Invinsense XDR+
With Patch Management and Deception Across Landscape, Invinsense ODS Makes it harder and confusing for adversaries to achieve their objectiveInvinsense XDR+
With Patch Management and Deception Across Landscape, Invinsense ODS Makes it harder and confusing for adversaries to achieve their objective -
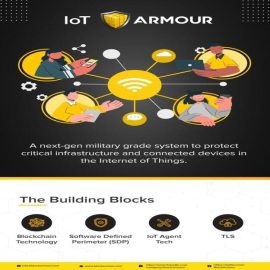
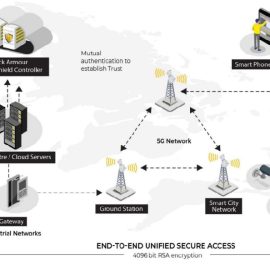
IoT Armour
With IoT Armour an organization can now move confidently into the journey of adopting IoT Sensors and Devices as part of their business processes. The solution utilizes a unique blockchain based digital identity for secure IOT device authentication and a policy based authorization to ensure only genuine devices and traffic is allowed to communicate with the IT based management systems. While reducing the attack surface available for attack by malware and ransomware.IoT Armour
With IoT Armour an organization can now move confidently into the journey of adopting IoT Sensors and Devices as part of their business processes. The solution utilizes a unique blockchain based digital identity for secure IOT device authentication and a policy based authorization to ensure only genuine devices and traffic is allowed to communicate with the IT based management systems. While reducing the attack surface available for attack by malware and ransomware. -
IOT Security Penetration Testing
“IOT security should be everyone’s Priority”. Using its unique testing methodology, professionally qualified security services professionals, and high-tech security testing laboratories, Kratikal can help you secure your IoT ecosystem, including IoT applications, cloud APIs, backend servers, and communication protocols.IOT Security Penetration Testing
“IOT security should be everyone’s Priority”. Using its unique testing methodology, professionally qualified security services professionals, and high-tech security testing laboratories, Kratikal can help you secure your IoT ecosystem, including IoT applications, cloud APIs, backend servers, and communication protocols. -
ISMAC Basic
$12.99$9.99 per endpoint/annumA versatile integrated SIEM that enables you to perform cybersecurity with an unified view.ISMAC Basic
A versatile integrated SIEM that enables you to perform cybersecurity with an unified view.$9.99Was $12.99Save $3 -
ISMAC Pro
$17.99$15.99 per endpoint/annumWith Case Management and a Threat Intelligence Feed you'll be able to better perform cybersecurity in complex environments with a broad mix of attack surfaces such as cloud, on-premises and personal endpoints.ISMAC Pro
With Case Management and a Threat Intelligence Feed you'll be able to better perform cybersecurity in complex environments with a broad mix of attack surfaces such as cloud, on-premises and personal endpoints.$15.99Was $17.99Save $2