Product categories
- Application Security
- Automotive Cyber Security
- Cloud Access Security Broker
- Cloud Security
- Cyber Security Services
- Data Security
- Endpoint Security
- Forensics
- Governance Risk Management & Compliance
- Infrastructure Security
- Mobile Security
- Network Security
- Password Manager
- Patch Configuration and Management
- Secure File Transfer
- Secure Web Gateway
- Security Information and Event Management
- Security Training Software
- Unified Threat Management
- User Security
- VAPT
-
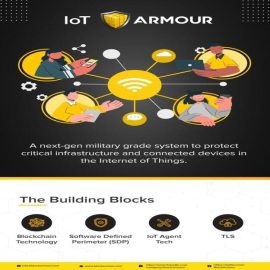
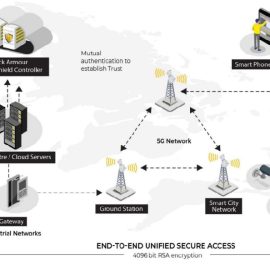
IoT Armour
With IoT Armour an organization can now move confidently into the journey of adopting IoT Sensors and Devices as part of their business processes. The solution utilizes a unique blockchain based digital identity for secure IOT device authentication and a policy based authorization to ensure only genuine devices and traffic is allowed to communicate with the IT based management systems. While reducing the attack surface available for attack by malware and ransomware.IoT Armour
With IoT Armour an organization can now move confidently into the journey of adopting IoT Sensors and Devices as part of their business processes. The solution utilizes a unique blockchain based digital identity for secure IOT device authentication and a policy based authorization to ensure only genuine devices and traffic is allowed to communicate with the IT based management systems. While reducing the attack surface available for attack by malware and ransomware. -
Kount Control
Kount Control prevents account takeover attacks by detecting high-velocity attacks from bots, credential stuffing, and other malicious activities. Plus, Kount Control customers can manage trusted devices and track failed login attempt data to improve account protection policies.
The account takeover solution combines machine learning, device intelligence , and customizable business policies to identify risky login behavior in real time. Whether from credential stuffing, card testing, bot attacks, or other abnormal activities, Kount Control challenges high-risk behavior and reduces friction for good customers.
Kount Control
Category: Fraud Prevention Identity Theft Detection Multi Factor Authentication | SKU: KOUNT-CONTROLKount Control prevents account takeover attacks by detecting high-velocity attacks from bots, credential stuffing, and other malicious activities. Plus, Kount Control customers can manage trusted devices and track failed login attempt data to improve account protection policies.
The account takeover solution combines machine learning, device intelligence , and customizable business policies to identify risky login behavior in real time. Whether from credential stuffing, card testing, bot attacks, or other abnormal activities, Kount Control challenges high-risk behavior and reduces friction for good customers.
-
Password Safe by BeyondTrust
Password Safe combines Privileged Account and Session Management (PASM) + Secrets Management capabilities, in one solution. Protect human and machine privileged identities, and your network, against account hijacking, credential re-use attacks, exposed hardcoded passwords, lateral movement, privilege escalation attacks, and more.- Credential, Key, & Secrets Management
- Real-Time Session Management
- Advanced Auditing & Forensics
Password Safe by BeyondTrust
Password Safe combines Privileged Account and Session Management (PASM) + Secrets Management capabilities, in one solution. Protect human and machine privileged identities, and your network, against account hijacking, credential re-use attacks, exposed hardcoded passwords, lateral movement, privilege escalation attacks, and more.- Credential, Key, & Secrets Management
- Real-Time Session Management
- Advanced Auditing & Forensics
-
PlainID Partner Manager
PlainID Partner Manager revolutionizes B2B Access Management (also known as Partner IAM or PIAM) by letting you manage your partners as “organizations,” while delegating admin capabilities, so your partners can manage their own users’ access.
PlainID Partner Manager
PlainID Partner Manager revolutionizes B2B Access Management (also known as Partner IAM or PIAM) by letting you manage your partners as “organizations,” while delegating admin capabilities, so your partners can manage their own users’ access.
-
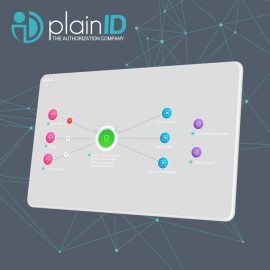
PlainID Policy Manager
PlainID’s Policy Manager gives you centralized management in a decentralized enforcement architecture. You get a focused view along with the ability to control who has access to what, across your digital landscape. It also provides improved visibility of access risks through advanced access control analytics. This allows a company to have predictive and prescriptive access controls, as well as run-time authorization enforcement using Policy-Based Access Control (PBAC) capabilities with workflows and SOD controls. It integrates with leading vendors in the IAM space such as SailPoint, Okta and Azure AD.
PlainID Policy Manager
PlainID’s Policy Manager gives you centralized management in a decentralized enforcement architecture. You get a focused view along with the ability to control who has access to what, across your digital landscape. It also provides improved visibility of access risks through advanced access control analytics. This allows a company to have predictive and prescriptive access controls, as well as run-time authorization enforcement using Policy-Based Access Control (PBAC) capabilities with workflows and SOD controls. It integrates with leading vendors in the IAM space such as SailPoint, Okta and Azure AD.
-
Privilege Access Management
Built to address the evolving privileged access use-case challenges, ARCON | PAM offers best-in-class access control features. A feature-rich solution, ARCON | PAM offers an IT security team with the deepest level of granular controls and Just-in-time (JIT) privileged access to enforce the principle of least privilege in any IT environment.
Trusted by more than 1000 global organizations, spanning wide-ranging industries, the enterprise-grade solution offers a best-fit architecture to ensure scalability, IT efficiency and privileged access security including compliance.
Privilege Access Management
Built to address the evolving privileged access use-case challenges, ARCON | PAM offers best-in-class access control features. A feature-rich solution, ARCON | PAM offers an IT security team with the deepest level of granular controls and Just-in-time (JIT) privileged access to enforce the principle of least privilege in any IT environment.
Trusted by more than 1000 global organizations, spanning wide-ranging industries, the enterprise-grade solution offers a best-fit architecture to ensure scalability, IT efficiency and privileged access security including compliance.
-
Privileged Access Management for System by Netand
HIWARE Privileged Access Management for System enables the complete management and supervision of users by controlling all accesses to and operations of the IT infrastructure operating system such as network and server, monitoring work details in realtime and saving log records.Privileged Access Management for System by Netand
HIWARE Privileged Access Management for System enables the complete management and supervision of users by controlling all accesses to and operations of the IT infrastructure operating system such as network and server, monitoring work details in realtime and saving log records. -
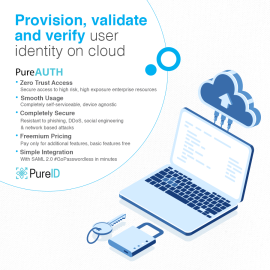
PureAUTH – The best Passwordless SSO Solution
PureAUTH is a SaaS based passwordless SSO platform. Completely self-serviceable & easy to deploy, PureAUTH is the most resilient passwordless authentication solution in the market.PureAUTH – The best Passwordless SSO Solution
PureAUTH is a SaaS based passwordless SSO platform. Completely self-serviceable & easy to deploy, PureAUTH is the most resilient passwordless authentication solution in the market. -
T2 COMMUNICATOR
$999.00T2 COMMUNICATOR secures mobile communication and data-at-rest. Engineered for organizations operating in the critical sectors. T2 COMMUNICATOR covers all critical vectors of attack:- hardware
- OS
- applications
- connectivity
T2 COMMUNICATOR
Category: Data-at-Rest Encryption Data-in-Motion Encryption Endpoint Security Messaging Security Mobile Communication Security Mobile Data Protection Mobile Device Management Secure File Transfer Zero trust |T2 COMMUNICATOR secures mobile communication and data-at-rest. Engineered for organizations operating in the critical sectors. T2 COMMUNICATOR covers all critical vectors of attack:- hardware
- OS
- applications
- connectivity
-
T2 COMMUNICATOR Dual OS
T2 COMMUNICATOR Dual is a unique Dual OS secure device for Professional and Professional use, eliminating the need of carrying multiple phones. It facilitates:
- Two completely separated and hardened operating systems
- Encrypted communication
- Secure file share and storage
- Malware, zero-click spyware, tracking, and IMSI-catcher protection
- Complete management of device permissions and policies
- An optional feature of self-hosting for unmatched security
T2 COMMUNICATOR and T2 COMMUNICATOR Dual
are engineered and trusted by organizations operating in critical sectors.
T2 COMMUNICATOR Dual OS
T2 COMMUNICATOR Dual is a unique Dual OS secure device for Professional and Professional use, eliminating the need of carrying multiple phones. It facilitates:
- Two completely separated and hardened operating systems
- Encrypted communication
- Secure file share and storage
- Malware, zero-click spyware, tracking, and IMSI-catcher protection
- Complete management of device permissions and policies
- An optional feature of self-hosting for unmatched security
T2 COMMUNICATOR and T2 COMMUNICATOR Dual
are engineered and trusted by organizations operating in critical sectors.
-
Valydate4U – A digital Onboarding Platform
Valydate4u Is a Complete 100% Paperless, Secure, KYC, VKYC, and Digital On-Boarding platform. Consent-Based, 100% Secured, Faceless, Fast (reduces time from 30mins To 2 Mins) Agent Or Self On-Boarding. Compliant With India’s RBI, Malaysia EKYC, And Other Global Standards.Valydate4U – A digital Onboarding Platform
Category: Fraud Prevention Identity and Access Management Identity Theft Detection User Authentication |Valydate4u Is a Complete 100% Paperless, Secure, KYC, VKYC, and Digital On-Boarding platform. Consent-Based, 100% Secured, Faceless, Fast (reduces time from 30mins To 2 Mins) Agent Or Self On-Boarding. Compliant With India’s RBI, Malaysia EKYC, And Other Global Standards. -
Zero Trust Isolation Platform
Zero Trust Isolation platform designed to contain, profile and stop lateral threat movement across any organization.Airgap ring fences every endpoint in a network of “1” to protect against lateral threat movement. AI/ML based technology continuously monitors devices and flows for anomaly detection and threat prevention.Zero Trust Isolation Platform
Zero Trust Isolation platform designed to contain, profile and stop lateral threat movement across any organization.Airgap ring fences every endpoint in a network of “1” to protect against lateral threat movement. AI/ML based technology continuously monitors devices and flows for anomaly detection and threat prevention.