Product categories
- Application Security
- Automotive Cyber Security
- Cloud Access Security Broker
- Cloud Security
- Cyber Security Services
- Data Security
- Endpoint Security
- Forensics
- Governance Risk Management & Compliance
- Infrastructure Security
- Mobile Security
- Network Security
- Password Manager
- Patch Configuration and Management
- Secure File Transfer
- Secure Web Gateway
- Security Information and Event Management
- Security Training Software
- Unified Threat Management
- User Security
- VAPT
-
PK Privacy
Business are required to keep up with an ever-changing privacy landscape, protecting the personally identifiable information they interact with. Meeting these requirements starts with understanding the organization's data as a whole, including indexing and correlating records based on specific criteria. PK Privacy gives organizations the power to automate data discovery and reporting mechanisms to assist with reducing the operational complications of privacy legislation.PK Privacy
Business are required to keep up with an ever-changing privacy landscape, protecting the personally identifiable information they interact with. Meeting these requirements starts with understanding the organization's data as a whole, including indexing and correlating records based on specific criteria. PK Privacy gives organizations the power to automate data discovery and reporting mechanisms to assist with reducing the operational complications of privacy legislation. -
Plurilock AI Cloud DLP
Plurilock AI Cloud DLP secures your users, software, and data seamlessly.- Single sign-on.
- Access control.
- Cloud least privilege.
- Data loss prevention.
- Workday control.
- Identity sanity.
Plurilock AI Cloud DLP
Plurilock AI Cloud DLP secures your users, software, and data seamlessly.- Single sign-on.
- Access control.
- Cloud least privilege.
- Data loss prevention.
- Workday control.
- Identity sanity.
-
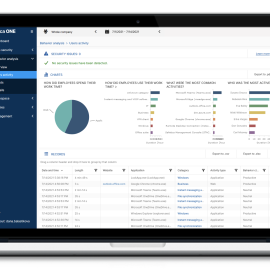
Safetica ONE Discovery+ UEBA
$22.00 – $30.00 for 1 yearIdentify how company data is used and where it is stored and sent, no matter where it resides or flows.- Windows and macOS support
- One-click integration with Microsoft 365
- File content inspection and classification
- Easy to upgrade to the full-featured data security platform
- Runs on bare metal or virtualized on-prem hosted, VM hosted in cloud
Safetica ONE Discovery+ UEBA
Identify how company data is used and where it is stored and sent, no matter where it resides or flows.- Windows and macOS support
- One-click integration with Microsoft 365
- File content inspection and classification
- Easy to upgrade to the full-featured data security platform
- Runs on bare metal or virtualized on-prem hosted, VM hosted in cloud
$22.00 – $30.00 for 1 year -
Safetica ONE Enterprise + UEBA
$45.00 – $62.00 for 1 yearEnterprise data security stack with maximum integration and workflow.- All-in-one data loss prevention & insider threat protection
- The easiest to implement & integrate enterprise DLP
- Advanced workspace control & behaviour analysis
- Very low hardware requirements for servers and device
Safetica ONE Enterprise + UEBA
Enterprise data security stack with maximum integration and workflow.- All-in-one data loss prevention & insider threat protection
- The easiest to implement & integrate enterprise DLP
- Advanced workspace control & behaviour analysis
- Very low hardware requirements for servers and device
$45.00 – $62.00 for 1 year -
Safetica ONE Protection + UEBA
$35.00 – $48.00 for 1 yearBased on the content inspection, internal risk analysis, and clear policies set up for all data channels, Safetica ONE Protection can recognize when somebody makes a mistake or takes chances with your sensitive data. Depending on which mode Safetica ONE is operating in, it can either block the risky activity, notify the admin, or remind the employee about the organization’s security guidelines.Safetica ONE Protection + UEBA
Based on the content inspection, internal risk analysis, and clear policies set up for all data channels, Safetica ONE Protection can recognize when somebody makes a mistake or takes chances with your sensitive data. Depending on which mode Safetica ONE is operating in, it can either block the risky activity, notify the admin, or remind the employee about the organization’s security guidelines.$35.00 – $48.00 for 1 year -
SCRUTINY SENSOR
Scrutiny predicts the true nature of files by emulating the static and dynamic behavior in a crypto caged environment and simultaneously training self-learning sensors at the same time to provide accurate verdicts along with detailed analysis in seconds. Our unique approach detects both known and unknown ransomware strains without any reliance on data engrams, centralized signature databases, etc. Also, this stands out as multi-tier, more innovative, and advanced than the other ransomware detection methods available.SCRUTINY SENSOR
Category: Cloud Security Data Security Email Security Endpoint Security Industrial Security Internet of Things Security Malware Detection and Analysis |Scrutiny predicts the true nature of files by emulating the static and dynamic behavior in a crypto caged environment and simultaneously training self-learning sensors at the same time to provide accurate verdicts along with detailed analysis in seconds. Our unique approach detects both known and unknown ransomware strains without any reliance on data engrams, centralized signature databases, etc. Also, this stands out as multi-tier, more innovative, and advanced than the other ransomware detection methods available. -
SecurDPS Discover and Classify
Comforte’s Discovery and Classification solution is a unique and proprietary passive network packet capture process to identify sensitive data (such as highly-regulated PII) flowing through the organization. This flow visibility enables our solution to identify repositories (databases, applications, file systems, and log files) where sensitive data resides. The solution then does a comprehensive scan of those repositories to get full visibility into the depth and breadth of the data environment. Finally, it analyzes and consolidates the data identified as a result of those scans in a structure that allows the user to see data lineage, respond to subject access requests, identify production data in non-production locations, and many other privacy, security, and data governance tasks.SecurDPS Discover and Classify
Comforte’s Discovery and Classification solution is a unique and proprietary passive network packet capture process to identify sensitive data (such as highly-regulated PII) flowing through the organization. This flow visibility enables our solution to identify repositories (databases, applications, file systems, and log files) where sensitive data resides. The solution then does a comprehensive scan of those repositories to get full visibility into the depth and breadth of the data environment. Finally, it analyzes and consolidates the data identified as a result of those scans in a structure that allows the user to see data lineage, respond to subject access requests, identify production data in non-production locations, and many other privacy, security, and data governance tasks. -
SecurDPS Enterprise
SecurDPS Enterprise allows organizations to take complete control of their sensitive data. Protecting sensitive data with a data-centric security approach helps your organization to comply with privacy regulations, reduce the risk of breaches and monetize valuable data – while improving your competitive advantage. Today SecurDPS Enterprise is protecting hundreds of millions of payment transactions, healthcare records, insurance records, and more, reliably running in business-critical environments.SecurDPS Enterprise
SecurDPS Enterprise allows organizations to take complete control of their sensitive data. Protecting sensitive data with a data-centric security approach helps your organization to comply with privacy regulations, reduce the risk of breaches and monetize valuable data – while improving your competitive advantage. Today SecurDPS Enterprise is protecting hundreds of millions of payment transactions, healthcare records, insurance records, and more, reliably running in business-critical environments. -
SecureTower
SecureTower is a 2 in 1 Solution: Data Leak Protection + Employee Monitoring. It's key features include: - Data leak protection - Staff efficiency and loyalty monitoring - Identification of potentially dangerous employees (risk analysis) - Business communications archive maintainingSecureTower
Category: Data Breach Protection Data Leakage Prevention Data Security File Content Security Secure File Transfer | SKU: STSecureTower is a 2 in 1 Solution: Data Leak Protection + Employee Monitoring. It's key features include: - Data leak protection - Staff efficiency and loyalty monitoring - Identification of potentially dangerous employees (risk analysis) - Business communications archive maintaining -
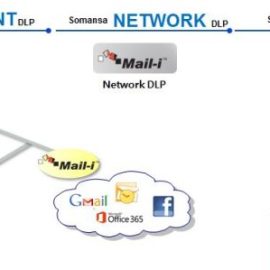
Somansa Data Leak Prevention
$70.00 – $120.00 / year• Data Discovery with classification • Data Leak Prevention • Encryption • Approval Management • Real time alerts and robust reporting
Protect Sensitive Data, Meet Regulatory Compliance Requirements.
Somansa is robust DLP, which can cater to all type of organizations & all requirements on DLP.
Endpoint Data Loss Prevention: Discover, Monitor, Prevent Sensitive Data Leakage on Your Endpoints
Network Data Loss Prevention: Secure Sensitive Data in Motion Before It Leaves Your Network
Somansa DLP: Prevent sensitive data in motion Emails, Cloud Services including Office 365 and Google G Suite and at rest, Removable Storage, Printing, Applications based on content, context aware policies.
Secure Data in Motion, Data at Rest, Encryption
Somansa Data Leak Prevention
Category: Data Discovery Data Leakage Prevention Data Security Digital Forensic Investigation and Computer Forensics | SKU: License• Data Discovery with classification • Data Leak Prevention • Encryption • Approval Management • Real time alerts and robust reporting
Protect Sensitive Data, Meet Regulatory Compliance Requirements.
Somansa is robust DLP, which can cater to all type of organizations & all requirements on DLP.
Endpoint Data Loss Prevention: Discover, Monitor, Prevent Sensitive Data Leakage on Your Endpoints
Network Data Loss Prevention: Secure Sensitive Data in Motion Before It Leaves Your Network
Somansa DLP: Prevent sensitive data in motion Emails, Cloud Services including Office 365 and Google G Suite and at rest, Removable Storage, Printing, Applications based on content, context aware policies.
Secure Data in Motion, Data at Rest, Encryption
$70.00 – $120.00 / year -
T2 COMMUNICATOR
$999.00T2 COMMUNICATOR secures mobile communication and data-at-rest. Engineered for organizations operating in the critical sectors. T2 COMMUNICATOR covers all critical vectors of attack:- hardware
- OS
- applications
- connectivity
T2 COMMUNICATOR
Category: Data-at-Rest Encryption Data-in-Motion Encryption Endpoint Security Messaging Security Mobile Communication Security Mobile Data Protection Mobile Device Management Secure File Transfer Zero trust |T2 COMMUNICATOR secures mobile communication and data-at-rest. Engineered for organizations operating in the critical sectors. T2 COMMUNICATOR covers all critical vectors of attack:- hardware
- OS
- applications
- connectivity