Product categories
- Application Security
- Automotive Cyber Security
- Cloud Access Security Broker
- Cloud Security
- Cyber Security Services
- Data Security
- Endpoint Security
- Forensics
- Governance Risk Management & Compliance
- Infrastructure Security
- Mobile Security
- Network Security
- Password Manager
- Patch Configuration and Management
- Secure File Transfer
- Secure Web Gateway
- Security Information and Event Management
- Security Training Software
- Unified Threat Management
- User Security
- VAPT
-
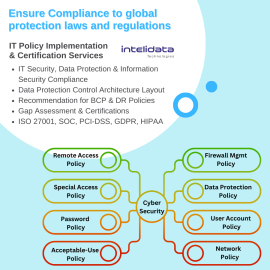
IT Policy and Certification Services by Intelidata
Review & Implementation of IS/IT Policies and IS/IT controls for their adequacy and effectiveness vis-à-vis frameworks/standards of ISO 27001:2022, IT Act 2008 & Cert-in guidelines.- IT Security, Data Protection & Information Security Compliance's Control Implementation
- Data Protection Control Architecture Layout as per new emerging Cyber Risks & Threats
- Recommendation for BCP & DR policies
- ISMS and Information Security Awareness Trainings for IT Staff
IT Policy and Certification Services by Intelidata
Review & Implementation of IS/IT Policies and IS/IT controls for their adequacy and effectiveness vis-à-vis frameworks/standards of ISO 27001:2022, IT Act 2008 & Cert-in guidelines.- IT Security, Data Protection & Information Security Compliance's Control Implementation
- Data Protection Control Architecture Layout as per new emerging Cyber Risks & Threats
- Recommendation for BCP & DR policies
- ISMS and Information Security Awareness Trainings for IT Staff
-
SOC2 Audit Services by Riskpro
Riskpro's unique approach to SOC2 audit engagement is sustained value addition to your business. Our readiness services enable you to remediate the control gaps in an efficient manner that not only help to get SOC 2 reports signed, but also improve productivity and efficiency in the business.SOC2 Audit Services by Riskpro
Riskpro's unique approach to SOC2 audit engagement is sustained value addition to your business. Our readiness services enable you to remediate the control gaps in an efficient manner that not only help to get SOC 2 reports signed, but also improve productivity and efficiency in the business.