-
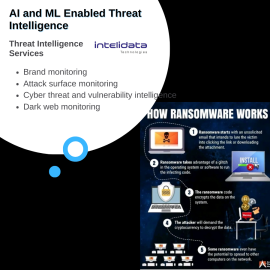
Threat Intelligence Services by Intelidata
Intelidata provides advanced threat intelligence with 360 degree coverage. The coverage includes:- Brand monitoring
- Social media monitoring
- Attack surface monitoring
- Cyber threat and vulnerability intelligence
- Cyber crime and dark web monitoring
- Supplier risk monitoring
Threat Intelligence Services by Intelidata
Intelidata provides advanced threat intelligence with 360 degree coverage. The coverage includes:- Brand monitoring
- Social media monitoring
- Attack surface monitoring
- Cyber threat and vulnerability intelligence
- Cyber crime and dark web monitoring
- Supplier risk monitoring
-
SOC as a Service by Intelidata
Intelidata Managed Services powered with SOC tools believes in taking a holistic approach to cyber security by gathering deep insights from endpoints, servers, network devices, applications, IOT and security systems and applying user identity, threat intelligence and vulnerability assessment to establish threat profile, generate threat indicators, raise essential alerts and offer remediation path – automated or triaged. In essence, the solution ensures multi-layered threat detection and response, relying on EDR, Network Behavior, Advanced Correlation (SIEM), Network Traffic Analysis, UEBA (ML based) and SOAR for an All-In-One experience that is organically and seamlessly fused together. It empowers SOC analysts to become more efficient and helps organizations to reduce MTTI and MTTR together providing continuous compliance for the business.SOC as a Service by Intelidata
Intelidata Managed Services powered with SOC tools believes in taking a holistic approach to cyber security by gathering deep insights from endpoints, servers, network devices, applications, IOT and security systems and applying user identity, threat intelligence and vulnerability assessment to establish threat profile, generate threat indicators, raise essential alerts and offer remediation path – automated or triaged. In essence, the solution ensures multi-layered threat detection and response, relying on EDR, Network Behavior, Advanced Correlation (SIEM), Network Traffic Analysis, UEBA (ML based) and SOAR for an All-In-One experience that is organically and seamlessly fused together. It empowers SOC analysts to become more efficient and helps organizations to reduce MTTI and MTTR together providing continuous compliance for the business. -
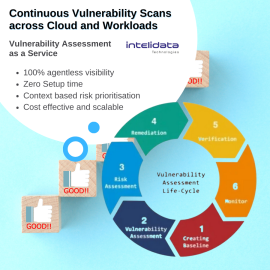
Vulnerability Assessment as a Service by Intelidata
Vulnerability Assessment Tool: Continuous vulnerability scan across clouds and workloads. Context-based prioritization based on exposure and impact. It can cover: Web App Security: Detect, patch security gaps in static websites, complex web apps and APIs Mobile App Security: Automated advanced security assessment of mobile applications - Android, iOS, WindowsVulnerability Assessment as a Service by Intelidata
Vulnerability Assessment Tool: Continuous vulnerability scan across clouds and workloads. Context-based prioritization based on exposure and impact. It can cover: Web App Security: Detect, patch security gaps in static websites, complex web apps and APIs Mobile App Security: Automated advanced security assessment of mobile applications - Android, iOS, Windows -
Cloud Security Services by Intelidata
CDL Cloud Security Services help clients secure their cloud migration and transformation journey to build a cyber- resilient and IT compliant cloud ecosystem. Our offerings include:- Cloud security strategy and architecture
- Cloud security assessment services
- Cloud managed security services
- Cloud security governance
- Cloud security solutions in implementation and support
Cloud Security Services by Intelidata
CDL Cloud Security Services help clients secure their cloud migration and transformation journey to build a cyber- resilient and IT compliant cloud ecosystem. Our offerings include:- Cloud security strategy and architecture
- Cloud security assessment services
- Cloud managed security services
- Cloud security governance
- Cloud security solutions in implementation and support
-
Virtual CISO as a Service by Intelidata
A V-CISO is your security point-of-contact for all security related issues, offering a direct line to experts as questions naturally arise. A virtual CISO will also respond to incidents, answer security-related questionnaires for your customers, and respond to data breach should that arise. In addition to ongoing and ad hoc support, a v CISO will tie into meetings when security expertise and guidance are needed. With our Cyber Security Consulting, we offer a no-compromise solution that eliminates new hire commitments while delivering the executive-level counsel needed to succeed. We’ll work alongside your management to best align security policies and practices with business objectives to advance your operational goals.Virtual CISO as a Service by Intelidata
A V-CISO is your security point-of-contact for all security related issues, offering a direct line to experts as questions naturally arise. A virtual CISO will also respond to incidents, answer security-related questionnaires for your customers, and respond to data breach should that arise. In addition to ongoing and ad hoc support, a v CISO will tie into meetings when security expertise and guidance are needed. With our Cyber Security Consulting, we offer a no-compromise solution that eliminates new hire commitments while delivering the executive-level counsel needed to succeed. We’ll work alongside your management to best align security policies and practices with business objectives to advance your operational goals. -
Forensic Audits by Intelidata
We help Enterprises to identify, prevent, detect, resolve, and protect their critical data from threats, crimes, frauds, and acts of terrorism arising due to vast proliferation and usage of Digital, Communication applications and artifacts in their personal and professional lives. We also provide assistance for legal enforcement to customer.
We also provide the 65B Certificate which is an important aspect to prove an innocent/guilty in the court of law.
Forensic Audits by Intelidata
We help Enterprises to identify, prevent, detect, resolve, and protect their critical data from threats, crimes, frauds, and acts of terrorism arising due to vast proliferation and usage of Digital, Communication applications and artifacts in their personal and professional lives. We also provide assistance for legal enforcement to customer.
We also provide the 65B Certificate which is an important aspect to prove an innocent/guilty in the court of law.
-
Red Team Assessment by Intelidata
Secure your applications against real-world vulnerabilities and run your business with confidence. Maximize security readiness by identifying real world vulnerabilities through rigorous intelligence driven security tests and replicating threat landscapes related to your business. Our Red Team exercises collate and analyze intelligent options which can be used by persistent attackers. We also test your existing security framework for any vulnerabilities to real time attacks.Red Team Assessment by Intelidata
Secure your applications against real-world vulnerabilities and run your business with confidence. Maximize security readiness by identifying real world vulnerabilities through rigorous intelligence driven security tests and replicating threat landscapes related to your business. Our Red Team exercises collate and analyze intelligent options which can be used by persistent attackers. We also test your existing security framework for any vulnerabilities to real time attacks. -
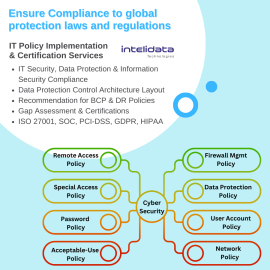
IT Policy and Certification Services by Intelidata
Review & Implementation of IS/IT Policies and IS/IT controls for their adequacy and effectiveness vis-à-vis frameworks/standards of ISO 27001:2022, IT Act 2008 & Cert-in guidelines.- IT Security, Data Protection & Information Security Compliance's Control Implementation
- Data Protection Control Architecture Layout as per new emerging Cyber Risks & Threats
- Recommendation for BCP & DR policies
- ISMS and Information Security Awareness Trainings for IT Staff
IT Policy and Certification Services by Intelidata
Review & Implementation of IS/IT Policies and IS/IT controls for their adequacy and effectiveness vis-à-vis frameworks/standards of ISO 27001:2022, IT Act 2008 & Cert-in guidelines.- IT Security, Data Protection & Information Security Compliance's Control Implementation
- Data Protection Control Architecture Layout as per new emerging Cyber Risks & Threats
- Recommendation for BCP & DR policies
- ISMS and Information Security Awareness Trainings for IT Staff
-
Network Scanning and Hardening by Intelidata
Network Scanning is a method of getting network information such as identification of hosts, port information, and services by scanning networks and ports. Our Scanning Methodology includes the following steps: -- Checking for live systems
- Discovering open ports
- Scanning beyond IDS
- Banner grabbing
- Scanning Vulnerabilities
- Network Diagram Proxies and more
Network Scanning and Hardening by Intelidata
Network Scanning is a method of getting network information such as identification of hosts, port information, and services by scanning networks and ports. Our Scanning Methodology includes the following steps: -- Checking for live systems
- Discovering open ports
- Scanning beyond IDS
- Banner grabbing
- Scanning Vulnerabilities
- Network Diagram Proxies and more
-
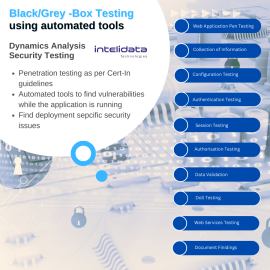
Dynamic Analysis Security Testing by Intelidata
Static Analysis Security Testing (SAST) services by Intelidata helps in finding vulnerabilities in the application while it is running. •Black/Grey-box security testing using automated tools; examines an application as it's running to find vulnerabilities that an attacker could exploit. •DAST will help in picking out deployment specific issues •Results from DAST and SAST can be compared to weed out false positivesDynamic Analysis Security Testing by Intelidata
Static Analysis Security Testing (SAST) services by Intelidata helps in finding vulnerabilities in the application while it is running. •Black/Grey-box security testing using automated tools; examines an application as it's running to find vulnerabilities that an attacker could exploit. •DAST will help in picking out deployment specific issues •Results from DAST and SAST can be compared to weed out false positives